by David Schwalenberg
March 9, 2016
The North American Electric Reliability Corporation (NERC) is a not-for-profit international regulatory authority whose mission is to assure the reliability of the bulk power system in North America. NERC Reliability Standards define the reliability requirements for planning and operating the North American bulk power system, which serves more than 334 million people. NERC is committed to protecting the bulk power system against cyber security compromises that could lead to misoperation or instability. The NERC Critical Infrastructure Protection (CIP) Standards provide a cyber security framework for the identification and protection of Bulk Electric System (BES) Cyber Systems, to support the reliable operation of the North American bulk power system.
The purpose of CIP-005 (Electronic Security Perimeter(s)) is "to manage electronic access to BES Cyber Systems by specifying a controlled Electronic Security Perimeter in support of protecting BES Cyber Systems against compromise that could lead to misoperation or instability in the BES." A critical aspect of protecting any network is protecting the network perimeter against external infiltration and attacks. In order to accomplish this, boundary protection devices and services such as firewalls, routers, anti-virus, and Intrusion Detection Systems (IDS) should be implemented within each network security perimeter. Proper network segmentation is crucial in the protection of network resources. Applying a multi-layered defense strategy will allow for multiple devices and services to protect the network in case one layer is breached. Attackers will target the weakest link on a network and pivot to other machines. If proper electronic security perimeters and protections are not established, compromise of one relatively unimportant machine can lead to catastrophic damage on critical systems.
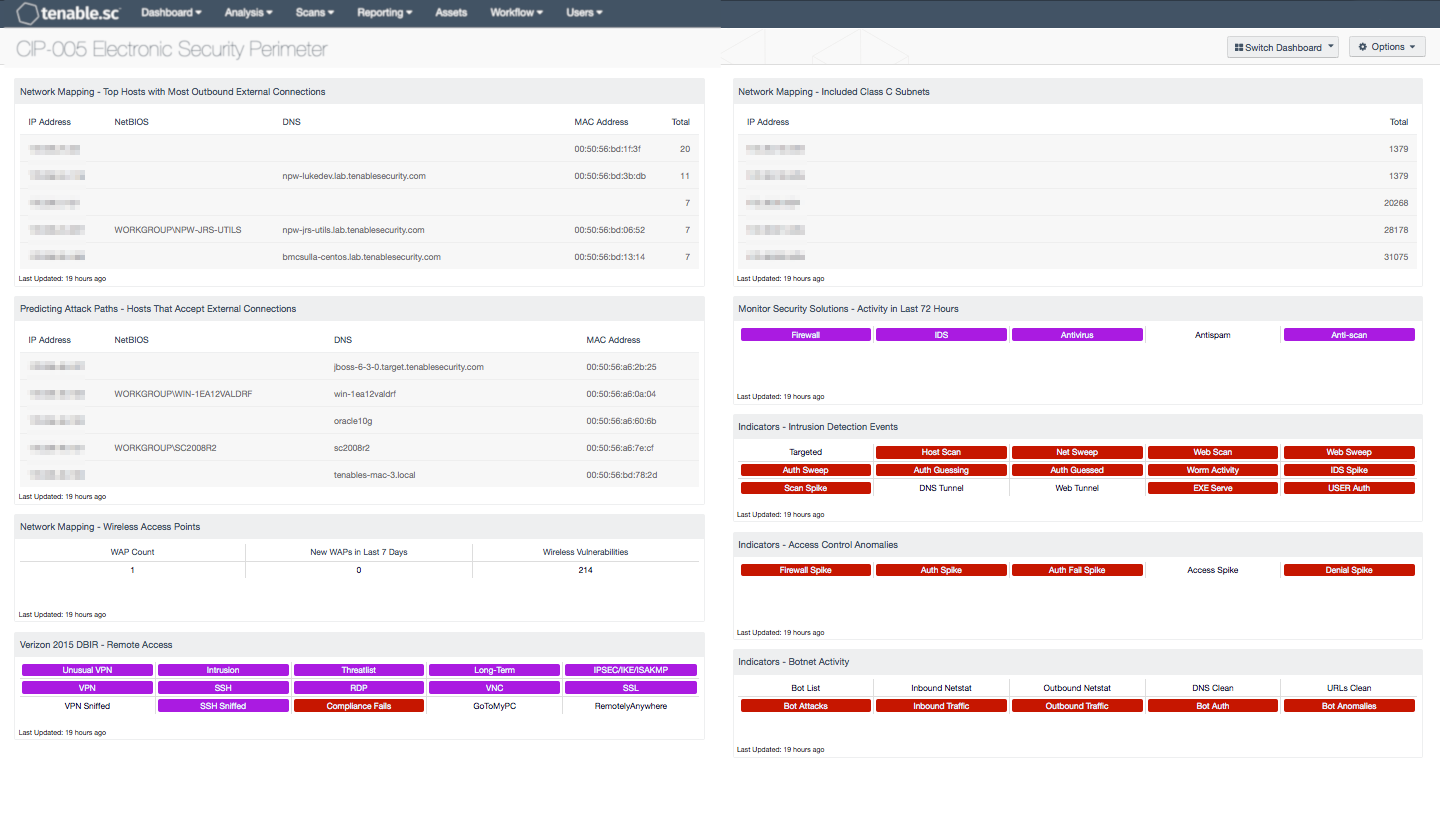
For organizations that are required to be CIP compliant, Tenable.sc Continuous View (CV) can lead the way to compliance. This dashboard can assist in identifying hosts with detected external connections, investigating remote and wireless access, and monitoring security solution activity. To monitor electronic access points and detect connections between systems inside the security perimeter and systems outside the security perimeter, IP address ranges for the internal network can be configured within the Nessus Network Monitor (NNM) and the Log Correlation Engine (LCE); see the product user guides. This dashboard can assist an organization in monitoring the electronic security perimeters and electronic access points on the network, which will aid in meeting the CIP-005 requirements and measures. Analysts can also use this dashboard to easily drill down and gain more detailed information.
The CIP standards recommend categorizing BES Cyber Assets into different impact categories. An asset's impact category is based on the adverse impact to BES reliability that would occur if the asset was unavailable, degraded, or misused. Once the impact categories of systems have been determined, asset groups in Tenable.sc CV can be used to group together machines in each impact category. Asset groups can then be applied to this dashboard to narrow the focus and enable more accurate reporting on systems in specific impact categories. For more information on using assets with dashboards, see How to Add Assets in SecurityCenter and How to Use Assets with Dashboards. A similar approach can be used to group assets within security perimeters. Alternatively, if the assets are in separate subnets, then subnet filters can be easily applied to narrow the focus of this dashboard.
This dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The dashboard requirements are:
- SecurityCenter 5.2.0
- Nessus 8.4.0
- PVS 5.8.1
- LCE 6.0.0
Tenable's Tenable.sc Continuous View (CV) is the market-defining continuous network monitoring solution. For Supervisory Control and Data Acquisition (SCADA) systems, where reliability and not interfering with normal operations is a concern, Tenable.sc CV includes passive vulnerability detection with Tenable’s Nessus Network Monitor (NNM), as well as log correlation with Tenable’s Log Correlation Engine (LCE). Where possible, active vulnerability detection and compliance scanning with Nessus can also be done. Using Tenable.sc CV, an organization will obtain the most comprehensive and integrated view of its SCADA network.
The following components are included in this dashboard:
- Network Mapping - Top Hosts with Most Outbound External Connections: This table presents information on those hosts with the most passively detected outbound external connections.
- Predicting Attack Paths - Hosts That Accept External Connections: This component utilizes plugin data to present an IP Summary of hosts that accept external connections.
- Network Mapping - Wireless Access Points: This component displays counts of actively and passively detected wireless access points (WAPs) and wireless vulnerabilities.
- Verizon 2015 DBIR - Remote Access: This matrix assists the organization in monitoring its remote access.
- Network Mapping - Included Class C Subnets: This table groups all the IP addresses discovered on the network into representative Class C subnets.
- Monitor Security Solutions - Activity in Last 72 Hours: This component assists in monitoring security solutions by presenting activity indicators for various security solutions: Firewall, IDS, Antivirus, Antispam, and Anti-scanning.
- Indicators - Access Control Anomalies: This component takes many of the various detection technologies for botnets, malicious file hashes, anomalous network traffic, spikes in system logs and continuous scanning activity and places them into one spot.
- Indicators - Intrusion Detection Events: This component takes many of the various detection technologies for botnets, malicious file hashes, anomalous network traffic, spikes in system logs and continuous scanning activity and places them into one spot.
- Indicators - Botnet Activity: This component indicates if the host is on a known botnet list.