Healthcare Security: Ransomware Plays a Prominent Role in COVID-19 Era Breaches

Ransomware is the root cause in a majority of the healthcare breaches analyzed.
As the ongoing COVID-19 pandemic continues to place unprecedented strain on global healthcare infrastructure, attackers are finding what was already an attractive target even more enticing. This unfortunate scenario has greatly expanded the attack surface for these malicious parties with the introduction of greater demand for remote services like telehealth, COVID-19 contact tracing app data, demand from medical manufacturing companies, and a race for medical research facilities to find a cure. An analysis of publicly disclosed breach data by the Tenable Security Response Team (SRT) reveals 237 breaches in the healthcare sector in the calendar year 2020. And the activity looks set to continue unabated in 2021, with 56 breaches already disclosed as of February 28. One finding is clear: ransomware attacks are not going away anytime soon.
Breaches Hit Healthcare Hard
The Tenable SRT monitors threat and vulnerability intelligence feeds to help drive and prioritize plugin coverage for Tenable products as well as keeping customers informed of the risks associated with vulnerabilities. For additional context, the team also monitors and tracks publicly disclosed breaches to understand how and when vulnerabilities are a factor. The Tenable 2020 Threat Landscape Retrospective (TLR) revealed a total of 22 billion records exposed as a result of 730 publicly disclosed breaches between January 2020 and October 2020, with healthcare being by far the most affected industry sector.
This comes as no surprise given the critical role healthcare infrastructure has had as a result of the COVID-19 pandemic.
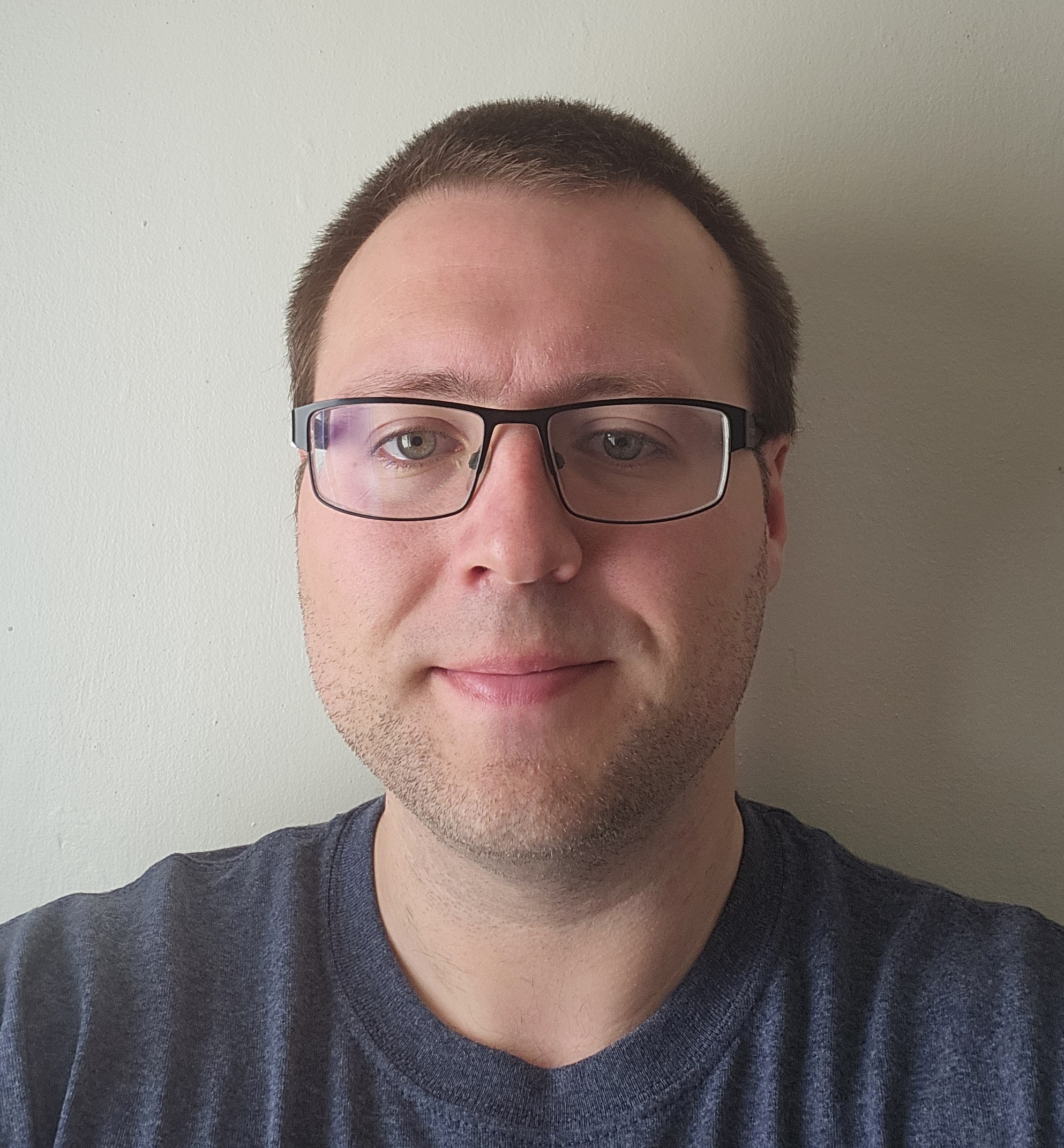
Breaches have long been a profitable business for threat actors, as highlighted in IBM's 2020 Cost of a Data Breach Report, which notes the average cost of a breach at $3.86 million. If that number weren't incentive enough for threat actors, the average cost of a breach for healthcare specifically was $7.13 million, with personally identifiable information (PII) valued at $150 per record making the industry a prime target.
Source: IBM Security Cost of a Data Breach Report 2020
Given the particular importance of the healthcare sector at a time of global pandemic, we felt it was important to expand on the original analysis provided in the TLR, which was limited by our publishing deadlines. In this blog, we examine the full 12 months of publicly disclosed breaches in 2020 and take a closer look at activity we've seen in the first two months of 2021. We've analyzed 293 breaches in the healthcare sector which were publicly disclosed between January 2020 and February 2021; records were confirmed to have been exposed in nearly 93% of these breaches. One obstacle with accurately tracking breaches is that public disclosures can occur days, months or even years after the event itself and, even then, the level of detail available may be scant. Of the 293 breaches known to have exposed records in the 14-month period we analyzed, 57.34% of the affected organizations have publicly disclosed how many records were exposed. The number of records exposed in this period reached a total of nearly 106 million records; 76.45% of these were disclosed in 2020. (Editor's note: At the time this blog was published, the ramifications of CVE-2021-26855, CVE-2021-26857, CVE-2021-26858 and CVE-2021-27065, four actively exploited Microsoft Exchange Server zero-days, are just beginning to emerge; Tenable Research is closely following developments related to this disclosure.)
Root Cause Analysis of Healthcare Breaches
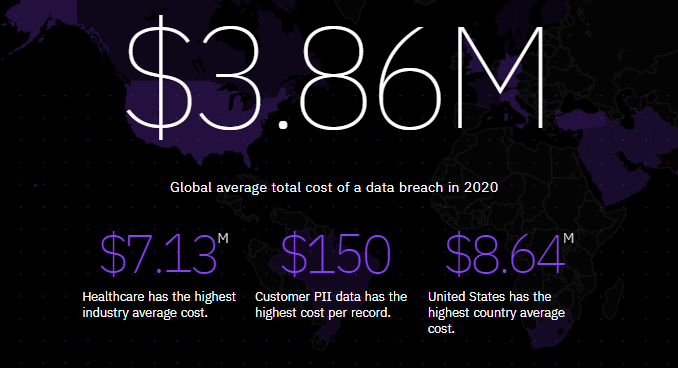
A root cause was reported in 93.17% of the healthcare breaches disclosed in the 14-month period we've analyzed. Among these, ransomware was by far the most prominent root cause of healthcare breaches, accounting for a whopping 54.95%. Other leading causes included email compromise/phishing (21.16%), insider threat (7.17%) and unsecured databases (3.75%).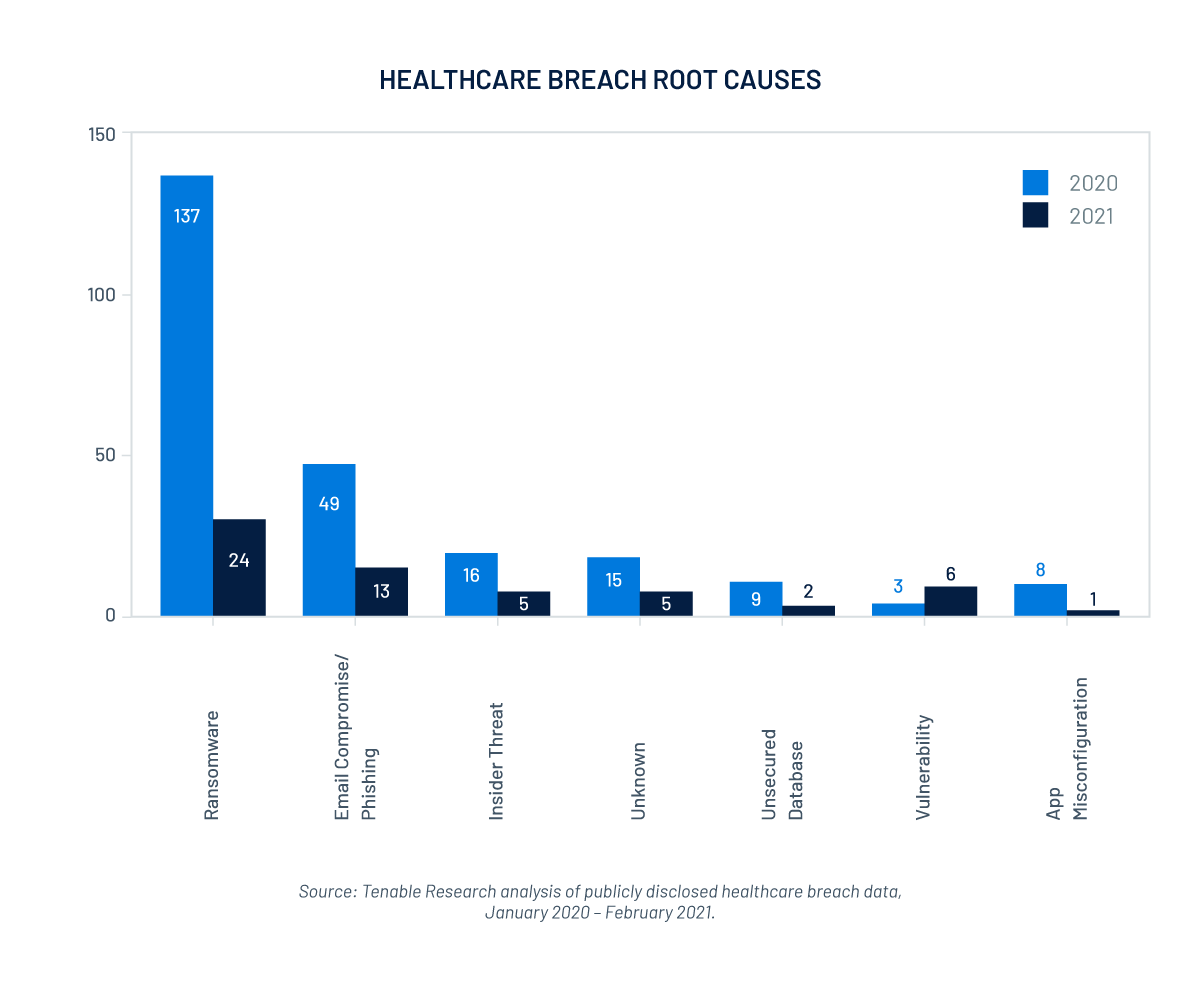
In some instances, breaches don't occur as a result of direct action against the victim or of their own actions, but rather occur as a result of a third-party breach. This occurs when a third-party vendor that you use is breached and, as a result, attackers gain access to your data which is stored in their system. In some circumstances, attackers exploit vendors to gain direct access to your system. In cases where the numbers were made public, our analysis shows that third-party breaches accounted for over a quarter of the breaches tracked and accounted for nearly 12 million records exposed. The breach of a single company accounted for over 10 million of these records. This breach has been linked back to 61 of their healthcare customers, with the number of exposed records expected to increase as more of these impacted customers disclose their numbers.
Some Healthcare Sectors Hit Worse Than Others
While the term "healthcare" is often used as if it describes a monolithic sector, there are in fact quite significant differences in the types of organizations operating within the broader healthcare category. In order to provide a more granular view, we've further segmented the data into 12 key classifications, which can be found in the table below. Healthcare systems — typically a collective of institutions, people and various resources across a geographical area — accounted for just over 30% of the breaches tracked. Because such systems can include multiple facilities spread across a number of campuses, the impact of 88 breaches is exponentially worse than if they had occurred in an individual, standalone facility such as a single hospital.
The top five healthcare categories experiencing the most breaches in the past 14 months were:
- Healthcare systems (30.03% of overall breaches)
- Hospital (19.11%)
- Mental health care/rehabilitation (6.14%)
- Medical clinic (5.12%)
- Government agency (4.10%)
| TOP 12 BREACHED SECTORS | ||||||
|---|---|---|---|---|---|---|
| Healthcare sector | Breach count | Share of overall breaches (%) | ||||
| 2020 | 2021 YTD |
Total | 2020 | 2021 YTD |
Total | |
| Healthcare system | 72 | 16 | 88 | 24.57% | 5.46% | 30.03% |
| Hospital | 43 | 13 | 56 | 14.68% | 4.44% | 19.11% |
| Mental health care / rehabilitation | 17 | 1 | 18 | 5.80% | 0.34% | 6.14% |
| Medical clinic | 11 | 4 | 15 | 3.75% | 1.37% | 5.12% |
| Government agency | 7 | 5 | 12 | 2.39% | 1.71% | 4.10% |
| Children's hospital | 9 | 0 | 9 | 3.07% | 0.00% | 3.07% |
| Healthcare software | 8 | 0 | 8 | 2.73% | 0.00% | 2.73% |
| Laboratory testing | 4 | 3 | 7 | 1.37% | 1.02% | 2.39% |
| Health insurance | 7 | 0 | 7 | 2.39% | 0.00% | 2.39% |
| Pharmaceuticals | 6 | 0 | 6 | 2.05% | 0.00% | 2.05% |
| Medical research | 5 | 1 | 6 | 1.71% | 0.34% | 2.05% |
| Herstellung medizinischer Produkte | 5 | 1 | 6 | 1.71% | 0.34% | 2.05% |
Source: Tenable Research analysis of publicly disclosed breaches, January 2020 - February 2021.
Ransomware - Root Cause of Healthcare Breaches
Ransomware accounted for 54.95% of breaches tracked, or 161 breaches. For 108 of these breaches, the culprits responsible never became publicly known. There are a variety of reasons for this, including:
- They were never identified.
- They decided to remain anonymous.
- The victims never publicly disclosed the details.
- They were never observed to have listed their victims or dumped their data on ransomware sites.
When it came to healthcare, Ryuk stood out above the rest, repeatedly appearing in breach disclosures and accounting for 8.64% of ransomware-related breaches, followed by Maze (6.17), Conti (3.7%) and REvil/Sodinokibi (3.09%), as shown in the chart below.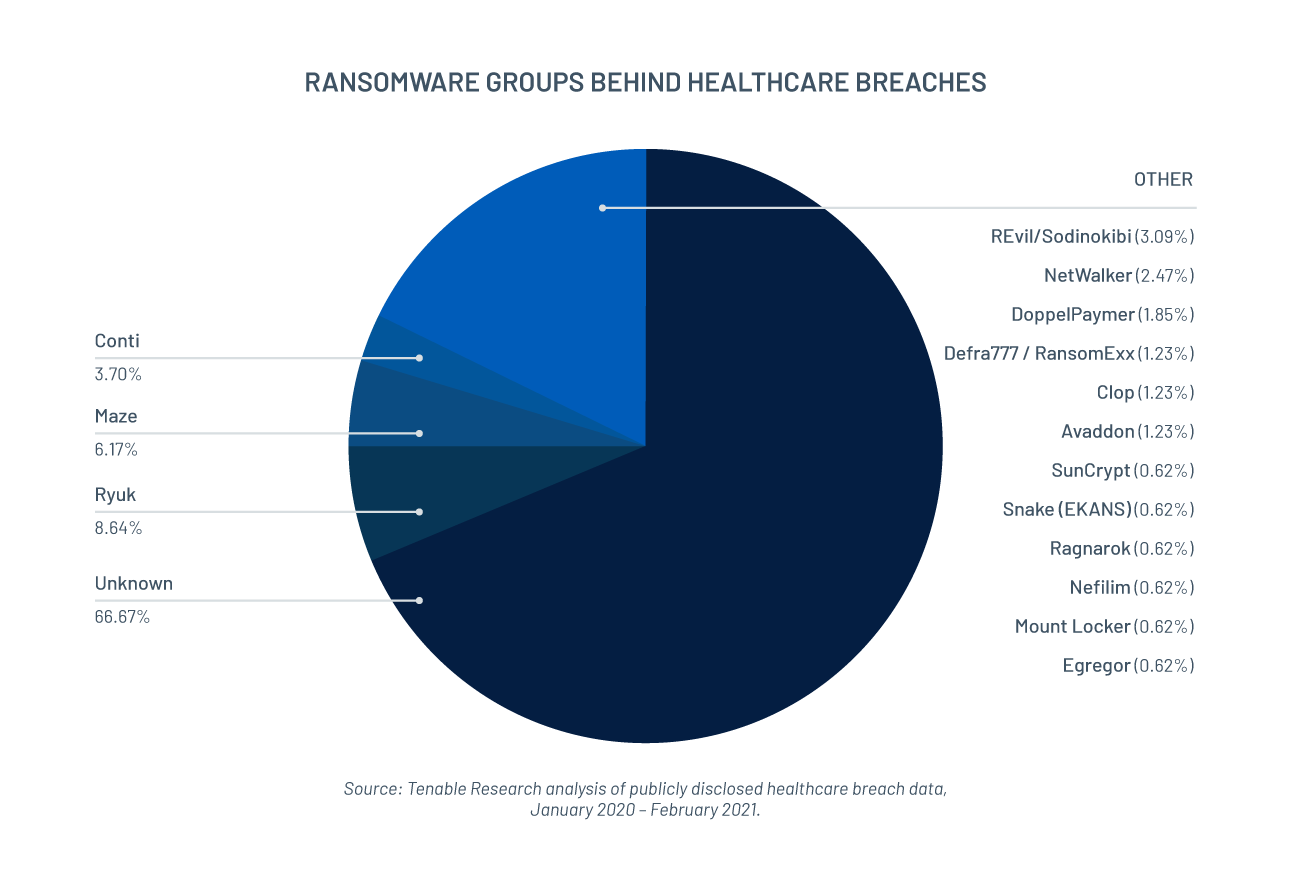
At one stage, towards the beginning of the pandemic, there was a glimmer of hope for the healthcare industry. Bleeping Computer reported that some ransomware groups claimed they would cease attacks against the sector. However, these ransomware gangs reneged on their promises, continuing to be tied to breaches throughout 2020, raising the question of whether ransom payments will be honored.
Unpatched Vulnerabilities Leveraged by Ransomware Groups
The root cause of the breaches tracked was predominantly disclosed as a result of ransomware or phishing/email compromise; it is a rare occurrence that exact methods used to breach a company are disclosed. Ransomware groups tend to favor leveraging certain attack vectors, so much so that they have their own fingerprints. Some are known to exploit vulnerabilities while others will utilize phishing/email compromise to establish an initial foothold before dropping malware or leveraging a vulnerability to gain further access to the victim's systems to deploy the ransomware.
Ryuk ransomware, the leading culprit for ransomware attacks against the healthcare industry, is known to favor a number of vulnerabilities, including those associated with Microsoft Server Message Block (SMB) as reported by Trend Micro. Analysis from researchers at The DFIR Report demonstrated how Ryuk threat actors went from sending an initial phishing email (similar to Conti) to controlling an entire domain using CVE-2020-1472 to elevate privileges less than two hours after the initial phish. This vulnerability, also dubbed "Zerologon," targeted a vulnerability in Netlogon which could allow attackers to hijack a Windows Domain Controller (DC). This vulnerability is highlighted as the top vulnerability in the Tenable 2020 TLR, so severe that Microsoft rolled out a second patch for it in February 2021 to enable Enforcement Mode by default.
In a recent article in SC Magazine, Jamie Hart, cyberthreat intelligence analyst at Digital Shadows, gives insight into Conti ransomware and how it has targeted healthcare facilities. Hart notes that Conti initially targeted victims with phishing emails before leveraging CVE-2020-0796, a wormable remote code execution (RCE) vulnerability in Microsoft SMBv3, to gain access to an admin account. Conti would use well-known open-source tools to enumerate and gain further access to the victim's networks. While Hart provides one observation of Conti ransomware, Coverware researchers highlight that they have observed Conti ransomware favoring the Remote Desktop Protocol (RDP). The Tenable 2020 TLR highlighted the increased use of RDP in the last year favored for remote working as it is included in the Windows operating system (OS). RDP, unfortunately, has a history of having critical vulnerabilities associated with the protocol, including CVE-2019-0708, dubbed "BlueKeep," CVE-2019-1181, CVE-2019-1182, CVE-2019-1222 and CVE-2019-1226, collectively named "DejaBlue."
Maze, prior to shutting down on November 1, 2020, was responsible for a number of attacks as highlighted by the above chart. Much like Conti and other ransomware groups, they are known to favor RDP as an attack vector but also have a history of targeting certain CVEs. These include CVE-2019-19781, a vulnerability in Citrix Application Delivery Controller (ADC) and Gateway, as reported by SHIELDX and CVE-2019-11510, a vulnerability in Pulse Connect Secure SSL VPN, as highlighted by Palo Alto Networks Unit 42. Both of these vulnerabilities made the top five vulnerabilities in the Tenable 2020 TLR despite being disclosed in 2019 as threat actors continue to target unpatched vulnerabilities.
Telehealth Solutions Expand the Attack Surface
The new norm of social distancing and doctors being very selective of the patients they see in person has resulted in an exponential rise in the use of telehealth for medical advice. Listening to Patient Data Security: Healthcare Industry and Telehealth Cybersecurity Risks, a study by Security Scorecard and DarkOwl, analyzed 148 of the most-used telehealth vendors from September 2019 to April 2020. The study found a staggering 30% increase per domain in their findings; below are some concerning stats directly from their report:
| Finding | Meaning |
|---|---|
| 117% increase in IP reputation security alerts | Malware infections — as part of successful phishing attempts and other attack vectors — ultimately cause IP reputation finding issues |
| 56% increase in endpoint security | Exploited vulnerabilities in endpoint security enable data theft |
| 16% increase in application security | Patients connect with telehealth providers using web-based applications including structured and unstructured data |
| 42% increase in FTP issues | FTP is an insecure network protocol that enables information to travel between a client and a server on a network |
| 27% increase in RDP issues | RDP is a protocol that allows for remote connections, which has seen increased usage since the widespread adoption of remote work |
Source: Listening to Patient Data Security: Healthcare Industry and Telehealth Cybersecurity Risks, a study by Security Scorecard and DarkOwl analyzing 30,000 healthcare organizations from September 2019 to April 2020.
While it's a positive to see a 65% increase in patching cadence findings reported, seeing an increase in telehealth IPs flagged as malicious, issues in insecure protocols and an uptick in vulnerabilities in telehealth being exploited do raise flags. It's clear from the Security Scorecard / DarkOwl study that there was an increase in exploiting telehealth in 2020 into the start of the pandemic. It would not be unfounded to assume telehealth was in the scopes of threat actors for the remainder of the year and going into 2021.
Vaccine Research and Production Prompts Cyberattacks
The research and development of COVID-19 vaccines introduced a prime target for threat actors and organizations involved in these efforts should be on high alert, as warned in a U.S. Cybersecurity and Infrastructure Security Agency (CISA) and Federal Bureau of Investigation (FBI) public service announcement towards the early stages of the pandemic. These attacks against vaccine research and production facilities prompted further advisories; the U.K.'s National Cyber Security Centre (NCSC) published one on July 16, 2020, in relation to an advanced persistent threat. The advisory highlighted APT29 as targeting COVID-19 vaccine development and is known to leverage the previously mentioned CVE-2019-19781 and CVE-2019-11510 but also CVE-2018-13379, a vulnerability in FortiGate SSL VPN. These facilities will continue to be targeted as long as they present financial opportunities, whether it's to halt production or research and hold victims to ransom or the act of cyber espionage with the intent to sell the data to the highest bidder.
The Prognosis for Healthcare Breaches
Whether threat actors leverage email compromise/phishing or vulnerabilities to gain an initial foothold in healthcare systems, it is highly probable that vulnerabilities will be the root cause of a system-wide compromise. The healthcare industry should take a two-pronged approach to cybersecurity:
- Prioritize vulnerabilities: identify and remediate vulnerabilities most likely to target and impact your organization.
- Address the root cause: while the human element is a factor in some instances, the majority of breaches can be prevented, or at a minimum impeded, by patching target vulnerabilities. The health of the network can be maintained through regular check-ups.
As explained above, the vulnerabilities being leveraged by these ransomware groups are targeted due to lack of patching, and overlap with vulnerabilities targeted by state-sponsored actors for the same reason.
It's clear healthcare will continue to be targeted in 2021 with breaches already making media headlines. Action needs to be taken to nullify the risk before more damage can be done.
Mehr erfahren
- Healthcare
- Malware
- Threat Intelligence
- Vulnerability Management
- Vulnerability Scanning