Leaked messages between Conti ransomware group members provide valuable insight into the vulnerabilities that are leveraged in attacks. Tenable.io enables security managers to determine their organization’s risk in relation to ransomware attacks. This dashboard identifies vulnerabilities in the environment that are being actively exploited by the Conti ransomware group and their affiliates.
The Conti ransomware group and their affiliates have had a particularly devastating impact on healthcare services, including at least 16 U.S. health and emergency networks. Conti attacked Ireland’s Health Service Executive (HSE), demanding a $20 million dollar ransom, which the HSE refused to pay, opting instead to shut down IT services for mitigation efforts.
Tenable’s 2021 Threat Landscape Retrospective report revealed that 24.7% of healthcare data breaches were the result of ransomware attacks, and ransomware itself was responsible for 38% of all breaches last year. The leaked data revealed that Conti and its affiliates have been exploiting a number of vulnerabilities. There are also reports that Conti and their affiliates have targeted vulnerabilities in the Fortinet FortiOS found in Fortinet’s SSL VPN devices to gain initial access to target environments.
Organizations are often breached from legacy vulnerabilities present in the IT infrastructure of small companies they have recently acquired. The analysis of the ContiLeaks data identifies the vulnerabilities that are being actively exploited, enabling security managers to prioritize mitigation.
The Security Response Team (SRT) of Tenable Research has analyzed the ContiLeaks data to ensure customers are fully informed of their vulnerability to Conti RaaS attacks. The SRT also provides breakdowns for the latest vulnerabilities in the Tenable Blog. Tenable Research has released over 165,000 plugins and leads the industry on CVE coverage. Tenable's SRT team continuously works to help organizations prioritize and create remediation plans for the new threats, which often leave very little time for reflection.
Security leaders need to SEE everything, PREDICT what matters most and ACT to address cyber risk and effectively align cybersecurity initiatives with business objectives. Tenable.io discovers and analyzes assets continuously to provide an accurate and unified view of an organization’s security posture. The requirement for this dashboard is: Tenable.io Vulnerability Management (Nessus).
Widgets
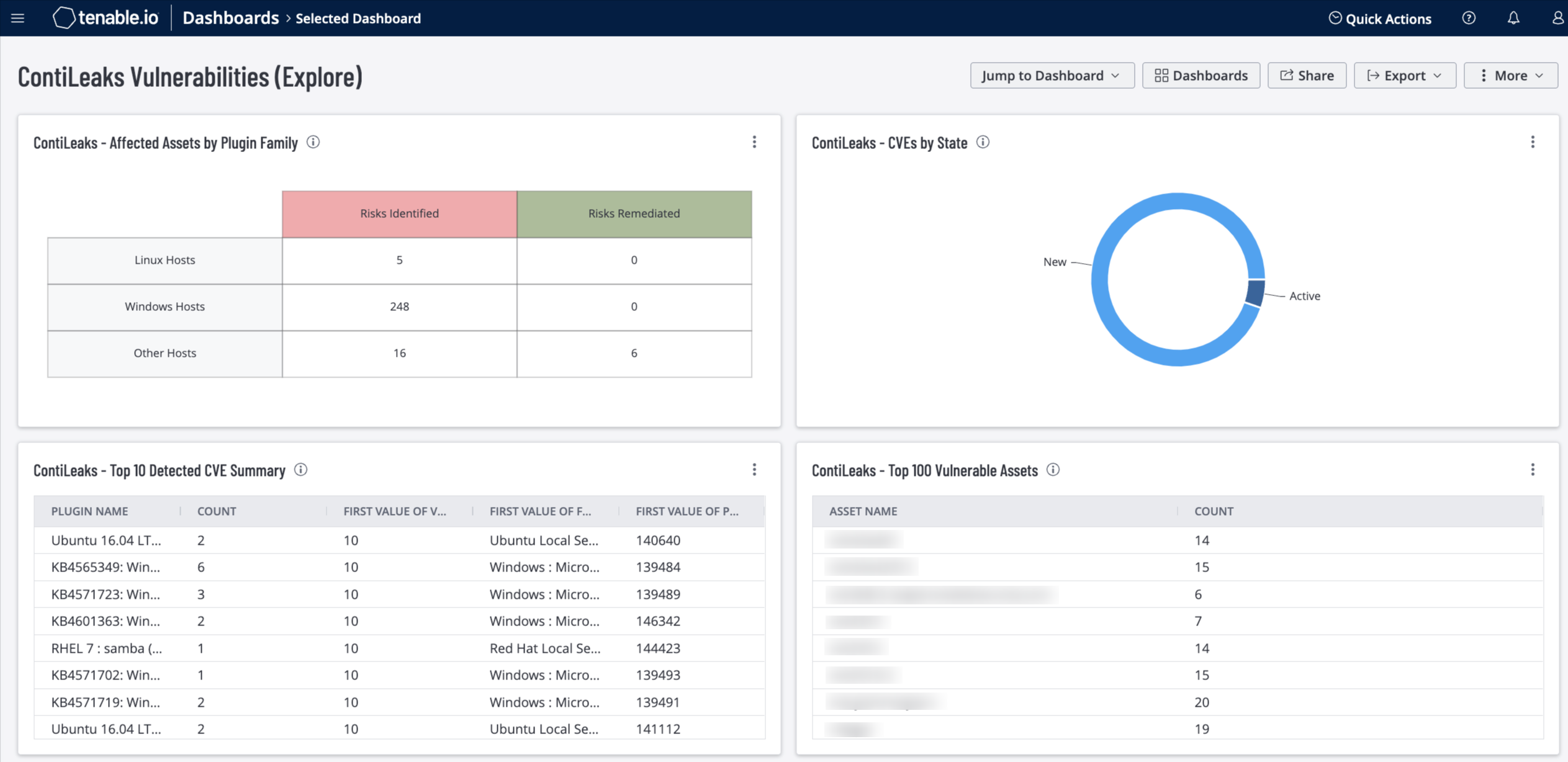
ContiLeaks - Affected Assets by Plugin Family: This widget uses the CVE and Plugin Family filters to display counts of assets that have been affected by ContiLeaks vulnerabilities. The number of vulnerabilities and assets that have been fixed are also displayed. Assets and vulnerabilities identified and remediated are shown using the referenced CVE. Rows for Linux, Windows, and other Operating Systems enumerate counts for the number of risks identified and mitigated. The requirement for this widget is: Tenable.io Vulnerability Management (Nessus).
ContiLeaks - CVEs by State: This widget uses known ContiLeaks CVEs to display the organization's current ContiLeaks mitigation state. The widget displays the New, Active, Fixed and Resurfaced ContiLeaks vulnerabilities. Vulnerability State is defined as:
- New – A vulnerability that has been detected one time.
- Active – A vulnerability that has been detected more than one time.
- Fixed – The vulnerability was present on a host, but is no longer present.
- Resurfaced – The vulnerability was previously marked as fixed on a host, but was detected again. When a vulnerability is Resurfaced, the state will not change from Resurfaced until the vulnerability is remediated, at which time the vulnerability will return to a Fixed state.
This data enables organizations to quickly visualize remediation efforts related to Contileaks vulnerabilities. The requirement for this widget is: Tenable.io Vulnerability Management (Nessus).
ContiLeaks - Top 10 Detected CVE Summary: This widget uses the known ContiLeaks CVEs as a filter to display assets with vulnerabilities related to ContiLeaks. Information is sorted by Vulnerability Priority Rating (VPR) in descending order, with the highest VPR scores at the top. The Plugin ID, Plugin Name, and Plugin Family that is associated with the identified ContiLeaks CVE is displayed, along with a count for each Plugin ID. The requirement for this widget is: Tenable.io Vulnerability Management (Nessus).
ContiLeaks - Top Vulnerable Assets: This widget uses the known ContiLeaks CVEs as a filter to display assets with vulnerabilities related to ContiLeaks. Information is filtered by vulnerabilities of high or critical severity that are exploitable, and is sorted by total vulnerabilities. Remediating assets at the top of the list will have the most impact in reducing risk. The requirement for this widget is: Tenable.io Vulnerability Management (Nessus).
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success