Mind the (Communication) Gap: How Security Leaders Can Become Dev and Ops Whisperers

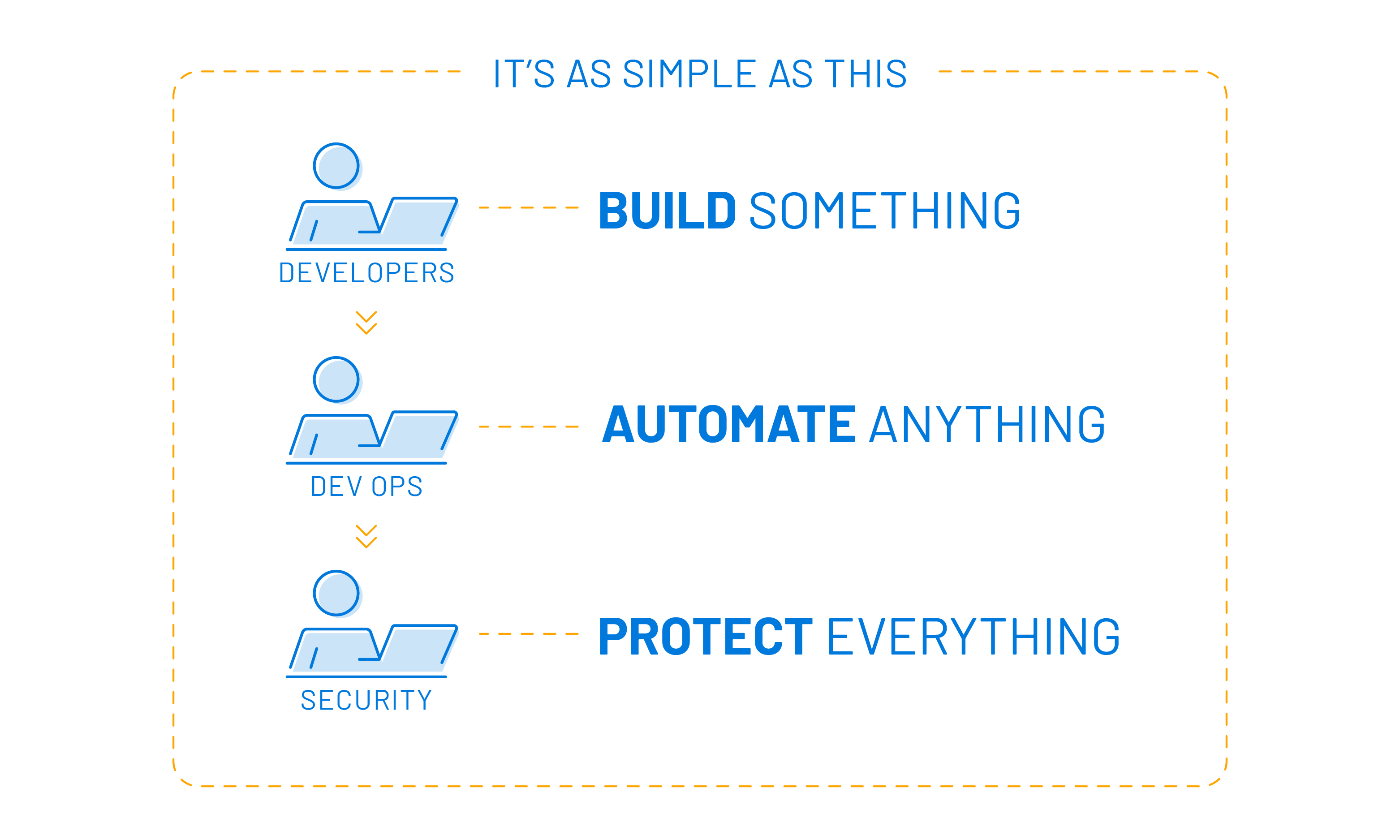
Developers, Ops and DevOps teams must incorporate security into their processes – often a hard sell. Here’s how security leaders can successfully align with them to weave security into their tools and workflows.
Establishing security controls across the enterprise used to be the exclusive realm of security teams. Not anymore. As a result, security leaders must get buy-in from developers, IT/OT Ops and DevOps teams to build security into their daily processes. The key is not just better communication, but engaging with these groups where they are, using the language they speak. As this post explains, security departments must transform from gatekeeping naysayers to business partners.
The changing world of enterprise security
As technology environments expand and evolve, incorporating a myriad of asset types and network architectures, including cloud platforms and IaC automation, more and more IT teams find themselves managing a wider array of critically important assets. Consequently, they must implement, adhere to and maintain security controls to protect the data, applications and assets they oversee. In order to protect these assets, it’s become imperative that development teams, DevOps groups and operations teams (both IT and OT) build security into their daily operations and tasks. But security isn’t the core competency of these teams – nor should we expect it to be! Their business goals, priorities and motivations are different – sometimes diametrically so – and that can create inherent resistance to the security team’s goals of mitigating risk throughout the organization.
Let’s start by outlining these differences and the ways to bridge the communication gap that often underpins the resistance these business units aim at the security team.
Why we do what we do
Let’s establish the motivations for the three key players in today’s technology landscape: Security, Development and DevOps. Security teams are driven by the familiar CIA triad of Confidentiality, Integrity and Availability. Controls put in place throughout the organization are designed to ensure one or more of these tenets. Protecting data from exposure, ensuring that assets aren’t compromised and building resiliency into the infrastructure are all key motivations for security.
Development teams aren’t motivated in the same way at all. While there may be some cursory acknowledgement of keeping systems up and running, security isn’t typically top of mind. Developers are builders at their core. They create new functionality, drive sales through new features and architect new software from the ground up. They see security as an obstacle to their goal of building something new. It’s hard to rapidly write and deploy code that delivers fancy new features to your end users when you have to conduct security scans, check in code for review and do whatever else the security team requires. It’s a recipe for immediate conflict: the need to balance efficient coding practices while deploying code that is secure, safe and free of errors that could lead to a compromise of the application.
DevOps teams, however, straddle the line between these groups, shuttling the code, applications and infrastructure from testbeds out into production. Like developers, DevOps sees security as an obstacle, but here, the primary driver isn’t necessarily creating something new, but rather, finding efficient ways to complete their tasks. This usually revolves around immense amounts of automation, which allows DevOps teams to be fast, flexible and able to address large-scale deployments with minimal effort. Here, security is seen as a hindrance to these automation processes because it requires multiple checks to ensure production deployments are safe and secured, and because it creates checkboxes to add to existing DevOps tasks which often aren’t as automated as their other workflows. This can dramatically slow down the deployment process, and that’s where the rub happens again.
Looking across the lines, there doesn’t seem to be an obvious place where these teams can intersect and find common ground. Or is there? Security leaders who know that these goals are far more aligned than most realize tend to succeed at breaking down resistance and building a stronger, more seamless security program that meaningfully reduces risk for the organization. It all starts with changing the message to align with what’s important to each of these teams.
WIIFM wins the day yet again
A common mistake security teams make with their communication programs is to assume that everyone understands that security is important, and they repeat a heavy security-focused message. But for most non-security business units in an organization, we often fail to explain security in terms that highlight WIIFM, i.e. “What’s In It For Me?”. Realistically, most non-security business units within an organization view security as an obstacle to their own efforts and commonly write it off as “that other team’s job”. Web content filters block websites. Endpoint security prevents the installation of fun games and applications. Email security stops people from clicking on enticing links promising lottery winnings, package delivery updates or tax solutions (seriously, please don’t click on anything like that). When security controls are seen as coming from “the department of no”, is it any wonder that developers and DevOps admins are hesitant to allow security controls into their domains?
Security doesn’t have to be “the department of no”, and the more we embrace security controls that sync with the way users, admins and engineers do business, the easier it is to show them what’s in it for them and the organization as a whole. So, let’s look at some recommendations across the People-Process-Tools triad where you can improve buy-in from your development and DevOps teams and tear down the obstacles that often prevent security teams from maturing and meeting their goals.
Table: People-Process-Tools Recommendations for Security Teams
Development Teams |
DevOps Teams |
|
|---|---|---|
|
People |
|
|
|
Process |
|
|
|
Tools |
|
|
Conclusion
At the end of the day, security professionals and leaders need to communicate with their audiences where the audiences themselves are, not where the security folks are. We must demonstrate that the security controls that we want to implement won’t be obstacles to the creation of new software features and functionality your development teams are focused on. We also need to show how those same controls won’t impede the speed and scalability that DevOps teams thrive on. If we are successful in communicating like this, security teams can move away from being seen as “the department of no”, and instead be recognized as a business partner who empowers the organization to be more operationally efficient while also reducing and mitigating risk to the core mission.
Learn More
- Read the white paper 3 Levels of Security Strategy for Business Risk Decisions
- Watch the on-demand webinar Cyber Leadership Lessons from the New World of Work: What's Next?
- Read the blog Aligning Cybersecurity and Business: Nobody Said It Was Easy
Learn more
- DevOps



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success