by Cody Dumont
October 20, 2014
Encrypting communications is a key part to network security, and SSL is a key component of securing data in motion. SecurityCenter CV is able to identify vulnerable systems before vendors issue patches by viewing scan data and event logs. The latest SSL vulnerability is called POODLE, aka Padding Oracle On Downloaded Legacy Encryption. While the vulnerability has a colorful name, do not let the severity fool you. The systems and users that are the most at risk are the ones that use captive portal pages in published hot spots, where Man-in-the-Middle (MitM) attacks are the most prevalent. This attack vector allows an attacker to extract data from secure HTTP connections. This could allow the attacker to do things such as access online banking or e-mail systems.
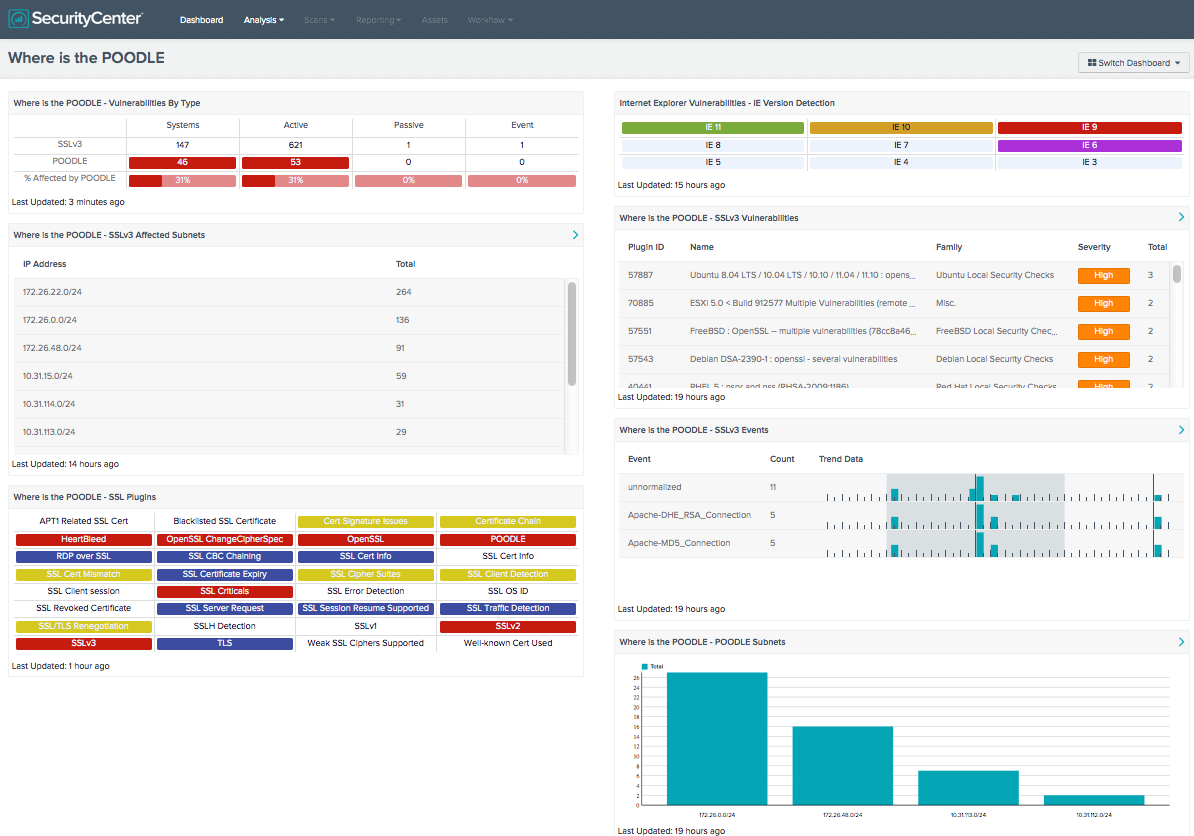
This dashboard provides several components, including the IE version and the SSL version used on the network. With IE 6 being vulnerable, the “Internet Explorer Vulnerabilities - IE Version Detection” component can identify the versions of IE present on the network, while the other components focus on the version of SSL used on the network.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Security Industry Trends.
The dashboard requirements are:
- SecurityCenter 4.8.1
- Nessus 5.2.7
- LCE 4.4.0
- PVS 4.0.2
SecurityCenter Continuous View allows for the most comprehensive and integrated view of network health and provides the most complete solution to identify emerging threats. By utilizing Nessus, the organization can actively discover SSL versions and browser versions. By using the Log Correlation Engine (LCE), the organization can perform deep log analysis detecting possible systems with elevated risk. The Passive Vulnerability Scanner (PVS) brings the ability to quickly identify vulnerabilities in real-time without directly accessing the clients or servers.
Where is the POODLE - Vulnerabilities By Type: This component displays information about systems on the network with vulnerabilities related to POODLE. The first row contains detected general SSLv3 vulnerabilities, the second row contains detected POODLE-specific vulnerabilities, and the third row calculates the percentage of the general SSLv3 vulnerabilities that are POODLE vulnerabilities. The first column shows the count of systems and the next four columns show the vulnerabilities detected actively and passively, as well as events.
Where is the POODLE - SSL Plugins: Several of the plugins that refer to SSL or certificates have been grouped into these indicators.
Where is the POODLE - SSLv3 Events: This component searches all events for events related to SSLv3 in the raw text. The table uses the Normalized Event summary tool to provide a 24 hour trend for each identified event. The events that relate to SSLv3 could mean either local servers are running SSLv3 or clients are connecting via SSLv3, both of which are not desirable. The table is sorted based on the number of events collected.
Where is the POODLE - SSLv3 Affected Subnets: This component displays the Class C subnets of the network that contain systems that have SSLv3 vulnerabilities. The columns displayed are subnet and vulnerability counts. Further investigation and remediation of these systems is needed. The table is sorted by the total number of vulnerabilities.
Where is the POODLE - POODLE Subnets: This component displays the Class C subnets of the network that contain systems that are vulnerable to POODLE. Each column displays a bar representing the number of vulnerable systems on each subnet. Further investigation and remediation of these systems is needed. The chart is sorted by the total number of affected systems.
Where is the POODLE - SSLv3 Vulnerabilities: This component displays a list of SSLv3 vulnerabilities, sorted by severity. The table contains the plugin ID, name, family, severity and total number of vulnerabilities.
Internet Explorer Vulnerabilities - IE Version Detection: The component detects the version of Internet Explorer. This component uses the Tenable products Nessus, PVS and LCE. The plugins that detect the version of Internet Explorer use user agent string detection or registry values. The colors in the indicator are set based on the version of Internet Explorer. For version 11, the color is set to white on green; the color for version 10 is black on orange. The colors white on red are set for the version 8 & 9, and all other versions are white on purple. The color indicates the severity of risk according to the version of Internet Explorer. The lower risk is green and orange, and the higher risks are red and purple.