Consolidate and Unify to Accelerate Your Security Efforts
CISOs want to shrink their cybersecurity tool stack and see improved interoperability among products so that they can draw actionable insights from uniform and normalized data. Here we explain why this is key for understanding your environment’s security posture and empowering you to make better decisions about mitigating risk.
As we covered recently on this blog, research from the Information Systems Security Association (ISSA) and analyst firm Enterprise Strategy Group (ESG) outlined the need for better interoperability between security tools. Which, if you’ve been in the infosec industry for more than a minute, has been a long-standing desire by security practitioners everywhere. As an industry, we’ve been very good at generating a lot of data, but less so at pulling it all together, normalizing it in an accurate and uniform way and ultimately making it easily digestible for analysts to determine what sort of direct action can and should be taken. It’s been the promise of many tools and technologies over the years: SIEM, SOAR, Behavioral Analysis, ML, AI, and many others. Heck, even basic log aggregation from years ago was supposed to fulfill this need. And yet, a couple of decades later, we’re still struggling with too much disparate data, desperately juggling spreadsheets to try and make sense of it all. And all in the name of trying to make smarter decisions about how and where we should focus on mitigating risk in our environments.
In truth, security vendors have gotten a lot better about providing APIs and other automated interfaces to allow for the movement of collected data to wherever their customers elect to pull it all together. But more attention must be paid to problematic underlying issues::
- A need to consolidate the sheer volume of tools needed to implement and manage a proper security program; and
- Uniform and normalized data for security findings to create a better, consistent understanding of the risk presented by a finding from different sources.
Consolidation of tools has become a prime topic of conversation more and more during discussions I have with CISOs across the globe. There’s a strong desire to find a balance between the 50+ tools the average organization manages in order to accomplish various monitoring and protection tasks and the one-size-fits-all approach that some vendors claim to offer, but don’t generally offer true best-of-breed levels of function and effectiveness. Vendors who understand this balance and get it right are the ones who innovate where it makes sense to do so, building upon their existing strengths and leveraging those new features, functions and products to enhance and empower their existing offerings instead of just adding another unrelated product to their portfolio. And security leaders lean heavily on word of mouth and recommendations from peers who work with vendors and products that actually deliver value without a lot of hype or fluff…so, vendors who aren’t credible or deliver what they claim are generally revealed across peer networks fairly quickly.
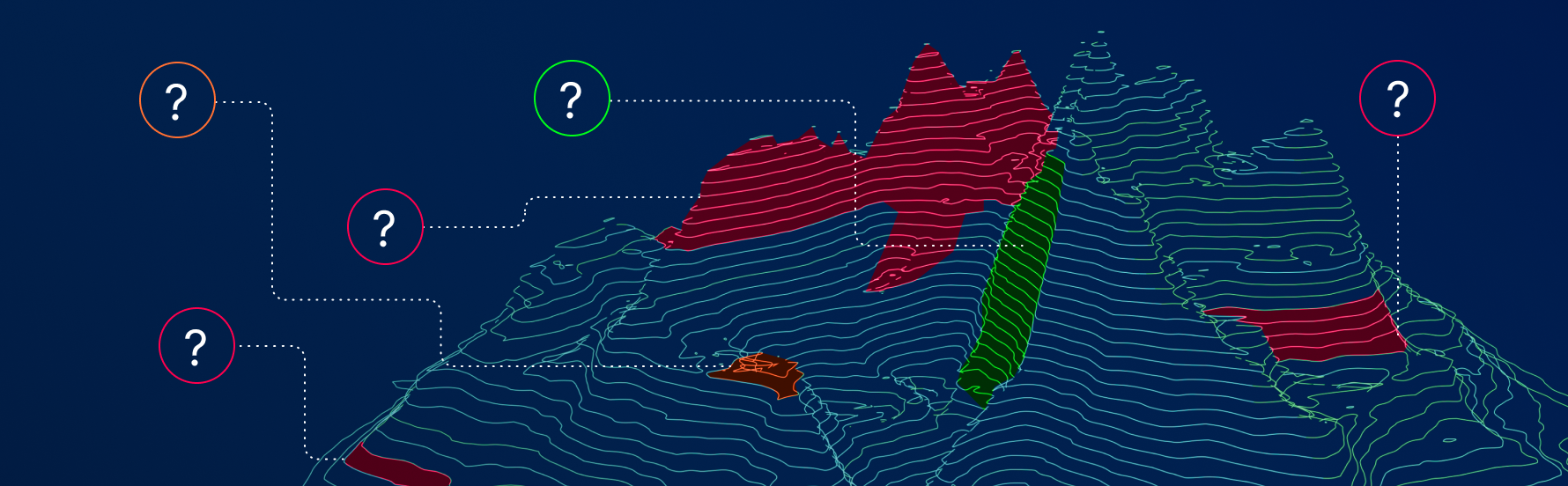
The other side of integrating tools is the challenge around unifying and normalizing the data that gets generated across all the different tools out there. Even if you were able to narrow down your security program’s tools to, let’s say, a dozen or so, there’s still a lot of different data types being gathered that have to somehow be compared in a way that makes it relate in a relevant way. Even if we were to consider two basic examples of security findings, such as a missing Windows patch and a SQL Injection vulnerability on a web application, it’s no simple task to put them side by side and determine which one is more of a risk to your environment than the other. They don’t share vulnerability identifiers like a CVE number, nor are they even the same type of vulnerability…so any effort around normalizing these findings together is hugely difficult. It’s something, frankly, the industry has been trying to accomplish to varying degrees for years. After all, even if you can bring all the data across your products together into a single place, it doesn’t do much good if it can’t help you understand the true security posture of your environment and empower you to make better decisions about mitigating risk for your organization.
So, interoperability isn’t the only thing to solve the challenge of bloating that CISOs are dealing with. Vendors have to go beyond simply providing API endpoints and export capabilities. Instead, they must bring disparate security data together, normalize and unify the risk factors so that each finding can be related to the others in a meaningful way and present those findings in a prioritized, easy-to-digest form. The focus needs to be creating that decision-making mechanism that allows security leaders to focus on identifying and mitigating risk and not spend their time sorting through mountains of spreadsheets and databases trying to make sense of all the data being generated by all the tools they don’t talk with each other.
Tenable has launched the Tenable One Exposure Management Platform, which unifies a variety of data sources into a single exposure view to help organizations gain visibility, prioritize efforts and communicate cyber risks. Check out these resources to learn more about it!
- Introducing the Tenable One Exposure Management Platform (blog)
- Exposure Management: Reducing Risk in the Modern Attack Surface (blog)
- 3 Real-World Challenges Facing Cybersecurity Organizations: How an Exposure Management Platform Can Help (white paper)
- From Risk-Based Vulnerability Management to Exposure Management (infographic)
- Exposure Management and the Future of Cybersecurity (LinkedIn Live)
Learn more
- Dashboards
- Exposure Management




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success