As organizations continue to evolve, wireless technologies are being integrated into existing networks to support employee mobility needs. Since wireless access can expose devices to unique threats, monitoring devices for access to suspicious or malicious wireless networks is essential. By integrating with Nessus, SecurityCenter Continuous View (CV) is able to monitor the wireless networks used by scanned hosts.
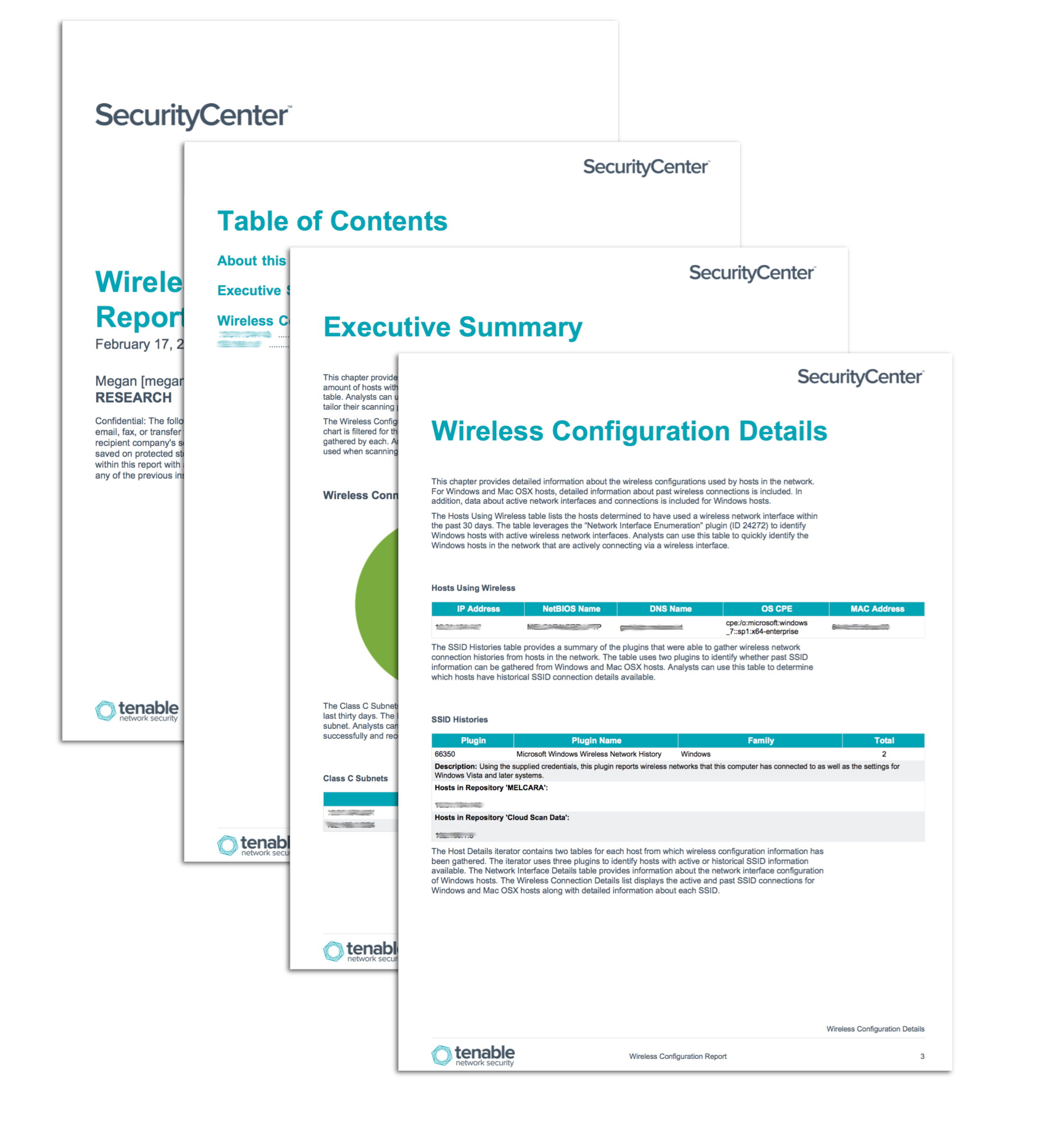
The Wireless Configuration report provides extensive information about the wireless networks accessed by scanned hosts in the organization. Several specific plugins are used to gather extensive details about wireless interfaces and SSID connections from Windows and Mac OS X hosts. Security teams can use this report to easily examine wireless configuration details for scanned hosts and tailor scanning policies in order to include additional hosts.
The chapters in this report present both a high-level overview and an in-depth analysis of the wireless configurations detected on hosts in the network. Charts and tables demonstrate which plugins were able to successfully gather wireless configuration details from scanned hosts. An iterator is used to provide extensive detail about wireless configurations of each host, including network interfaces and SSID histories. The report can be easily altered to address subnets or assets of particular concern. Security teams can use this detailed report to identify and monitor the wireless connections and configurations of hosts in the organization.
This report is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards and assets. This report can be easily located in the SecurityCenter Feed under the category Discovery & Detection. The report requirements are:
- SecurityCenter 5.2.0
- Nessus 6.5.4
SecurityCenter Continuous View (CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. Nessus is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. By integrating with Nessus, SecurityCenter CV provides the most comprehensive view of network security data.
The following chapters are in this report:
- Executive Summary: This chapter provides a high-level overview of the wireless configurations of hosts on the network.
- Wireless Configuration Details: This chapter provides detailed information about the wireless configurations used by hosts in the network.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success