Exploits leveraged in attacks are imported into various tools and services when the attack is made public. Common exploit frameworks are easy to obtain and are used by both security researchers and malicious attackers. Security analysts can effectively reduce risk to the organization by analyzing an exploit's source tool and the most common targets. Tenable Vulnerability Management provides security operations teams a centralized view of common vulnerabilities and exploit frameworks present in the organization’s environment.
The Cyber Security Framework (CSF) category ID.RA (Risk Assessment) provides guidance to organizations on cyber risk and helps to define recommended actions for the security operations team. The ID.RA-1 category states requirements for the National Institute of Standards and Technology (NIST) 800-53 control CA-8 Penetration Testing. The control states 'Penetration testing is a specialized type of assessment conducted on information systems or individual system components to identify vulnerabilities that could be exploited by adversaries.' Some security teams leverage exploitation frameworks such as Core Impact, Canvas or others to help with this control. Tenable Vulnerability Management identifies which vulnerabilities are exploitable by different frameworks. Exploit frameworks do not always have the same exploits, and, while there may be some overlap, a correlated view of exploits in the environment from multiple frameworks helps organizations understand which exploit frameworks pose the greatest threat.
Many organizations conduct internal red team (offense) and blue team (defense) exercises to gain insight into their exposures to attackers and their ability to defend against attacks. These exercises are a great way to harden the infrastructure before an official audit or malicious attack occurs. Having detailed information about exposures in the infrastructure before commencing such exercises enables red and blue teams to more effectively uncover exposures that a sophisticated auditor or attacker would find. While exploit frameworks are a great start, they are simply tools that are only as effective as the skill of the person using them. Using this dashboard to drill down into the Explore Findings view displays other attributes such as CPE, VPR Key Drivers, and CVSS Vectors. Each of these filters helps red and blue teams to narrow their focus and discover risks that may require prioritization over other vulnerabilities.
Vulnerabilities can also be widely exploited shortly after publication as malware authors reverse engineer the fix and develop '1-day exploits' that can be used to attack organizations. Tenable Vulnerability Management easily identifies assets most vulnerable to malware and other exploitation frameworks. This dashboard provides the necessary context to understand which assets are vulnerable to malware exploitation. Organizations can better communicate cyber risk to the business by supplying context and associated metrics.
Security leaders need to SEE everything, PREDICT what matters most, and ACT to address cyber risk and effectively align cybersecurity initiatives with business objectives. Tenable Vulnerability Management discovers and analyzes assets continuously to provide an accurate and unified view of an organization's security posture. The requirement for this dashboard is: Tenable Vulnerability Management (Nessus, NNM).
Widgets
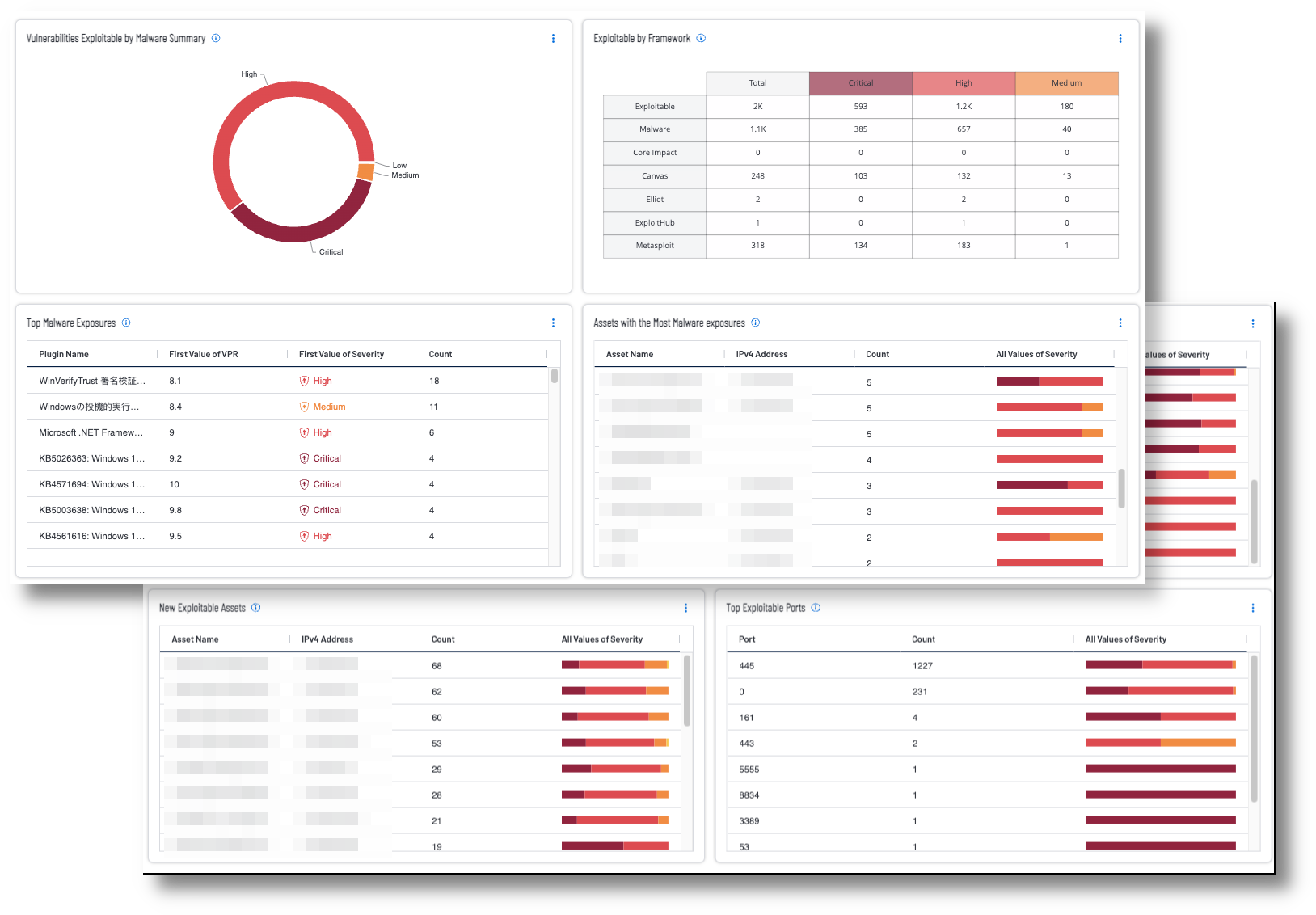
Vulnerabilities Exploitable by Malware Summary – This widget displays a summary of the top vulnerabilities that are exploitable by malware. Tenable recommends prioritizing remediation to reduce the organization's overall attack surface. The requirement for this widget is: Tenable Vulnerability Management (Nessus, NNM).
Exploitable by Framework – This widget provides a summary of exploitable vulnerabilities by framework. Exploitation frameworks, such as Metasploit, and Canvas, are designed to detect and exploit software and hardware vulnerabilities in target systems. This matrix helps security teams discover risks that may require prioritization over other vulnerabilities. The requirement for this widget is: Tenable Vulnerability Management (Nessus, NNM).
Top Malware Exposures – This widget displays the most prevalent, active Malware exposures. The widget will filter to show only active, resurfaced, or new plugins; filter out any accepted risks and use the exploitable filter to display only plugins that can be exploited by malware. The requirement for this widget is: Tenable Vulnerability Management (Nessus, NNM).
Assets with the Most Malware Exposures – This widget displays the hosts with the most active Malware exposures. The widget will filter to show only active, resurfaced, or new plugins; filter out any accepted risks and use the exploitable filter to display only plugins that can be exploited by malware. The requirement for this widget is: Tenable Vulnerability Management (Nessus).
Top Exploitable Windows Assets – This widget displays a list of the top Windows assets that have exploitable vulnerabilities, with a Vulnerability Priority Rating (VPR) greater than or equal to 7.0. Security technicians can use this information to focus mitigation efforts by operating system. This allows technicians to notify the asset administrator of the threats posed to their assets. The requirement for this widget is: Tenable Vulnerability Management (Nessus, NNM).
Top Exploitable Linux Assets – This widget displays a list of the top Linux/Unix assets that have exploitable vulnerabilities, with a Vulnerability Priority Rating (VPR) greater than or equal to 7.0. Security technicians can use this information to focus mitigation efforts by operating system. This allows technicians to notify the asset administrator of the threats posed to their assets. The requirement for this widget is: Tenable Vulnerability Management (Nessus, NNM).
New Exploitable Assets – This widget displays the top 20 Assets with Exploitable Vulnerabilities that have been newly discovered. Vulnerabilities marked as New have not been seen before on an asset. A vulnerability can be marked as New if that vulnerability had not been discovered before in a scan, or if that vulnerability was recently published and discovered on a new scan. This allows technicians to see previously secure assets with new exploitable vulnerabilities. The vulnerability will be marked Active when seen on a subsequent scan. The requirement for this widget is: Tenable Vulnerability Management (Nessus, NNM).
Top Exploitable Ports – This widget displays the top exploitable ports found in the environment, sorted from the highest count to lowest. The first column identifies the port number that is exploitable, followed by a count of how many were discovered. Hovering over the “All Values of Severity” bar displays a percentage of severity level discovered for each port. The requirement for this widget is: Tenable Vulnerability Management (Nessus, NNM).
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success