Daten in Maßnahmen umsetzen: Intelligence-gestütztes Schwachstellenmanagement

Schwachstellen im Kontext zu priorisieren, war schon immer eine Herausforderung für Schwachstellenmanagement-Teams – und angesichts der stetig wachsenden Zahl veröffentlichter CVEs wird diese Aufgabe nicht leichter. Um Abhilfe zu schaffen, sind viele Unternehmen gezwungen, in Tools und Services zu investieren, um ihre Umgebungen mit verschiedenen Intelligence-Daten und Tools zu schützen. In diesem Blog erläutern wir, wie Tenable Vulnerability Intelligence und Exposure Response Unternehmen helfen, Intelligence-gestützte Entscheidungen zu treffen, damit sie ihre Maßnahmen besser priorisieren und umsetzen können.
Schwachstellenmanagement (Vulnerability Management, VM) stellt für Unternehmen ein scheinbar unüberwindbares Hindernis dar: Wie soll man mit der massiven und schnell wachsenden Zahl veröffentlichter CVEs (Common Vulnerabilities and Exposures) umgehen? Als Unternehmen, das von Anfang an auf Schwachstellenmanagement fokussiert war, hat auch Tenable mit diesem Problem zu kämpfen, jedoch mit einer zusätzlichen Komplikation: Aufgrund unseres breiten Kundenstamms müssen wir so viele CVEs wie möglich in möglichst vielen Produkten abdecken und gleichzeitig den Risikokontext, die Genauigkeit und die Zuverlässigkeit wahren.
Die Lösung besteht nicht in dem Versuch, jede mögliche Kombination von CVEs und betroffenen Produkten zu überprüfen. Stattdessen müssen wir die kritischsten Schwachstellen mit genauem und gezieltem Kontext priorisieren. Damit diese Entscheidungen schnell und präzise getroffen werden können, nutzt Tenable eine riesige, durchsuchbare Datenbank mit Informationen zu Schwachstellen, die sowohl aus externen Quellen als auch von Tenable Research stammen. Es handelt sich dabei um dieselbe Datenquelle, die eine neue Funktion im Tenable Vulnerability Management-Produkt namens Vulnerability Intelligence unterstützt. Diese Funktion soll Kunden dabei helfen, ihre Vulnerability Management-Programme besser zu operationalisieren und schnelle datengestützte Priorisierungsentscheidungen zu treffen.
Die Lage ist schlecht und wird immer schlimmer
Das Jahr 2024 ist erst zur Hälfte um, und wir sind auf dem besten Weg, die Zahl von 30.000 veröffentlichten CVEs in diesem Jahr zu überschreiten. Erschwerend kommt hinzu, dass wir immer mehr CVEs in den zugrunde liegenden Komponenten, Frameworks und Sprachbibliotheken finden. Das bedeutet, dass Unternehmen nicht nur eine einzelne Anwendung beheben, sondern stattdessen alle Anwendungen, die die betreffende anfällige Komponente verwenden, aufspüren und beheben müssen.

Nutzung von Tenable Vulnerability Intelligence zur Ausarbeitung von Priorisierungsstrategien
Bei Tenable bemühen wir uns nicht nur täglich darum, aktuelle Schwachstellen-Abdeckung für Versionen wichtiger Produkte bereitzustellen, sondern sind auch ständig auf der Suche nach der nächsten bedeutenden Schwachstelle, um sicherzustellen, dass wir so schnell wie möglich reagieren können. Die Auswertung der Kontextdaten aus Tenable Vulnerability Intelligence ist entscheidend dafür, dass wir schnell fundierte Entscheidungen treffen können. Angesichts des beträchtlichen Rückstands, der bei der National Vulnerability Database (NVD) zu verzeichnen ist, können wir dank des Tenable Vulnerability Intelligence-Datenbestands über die neuesten Schwachstellen und Risiken auf dem Laufenden bleiben, da wir nicht nur an eine einzige Datenquelle gebunden sind.
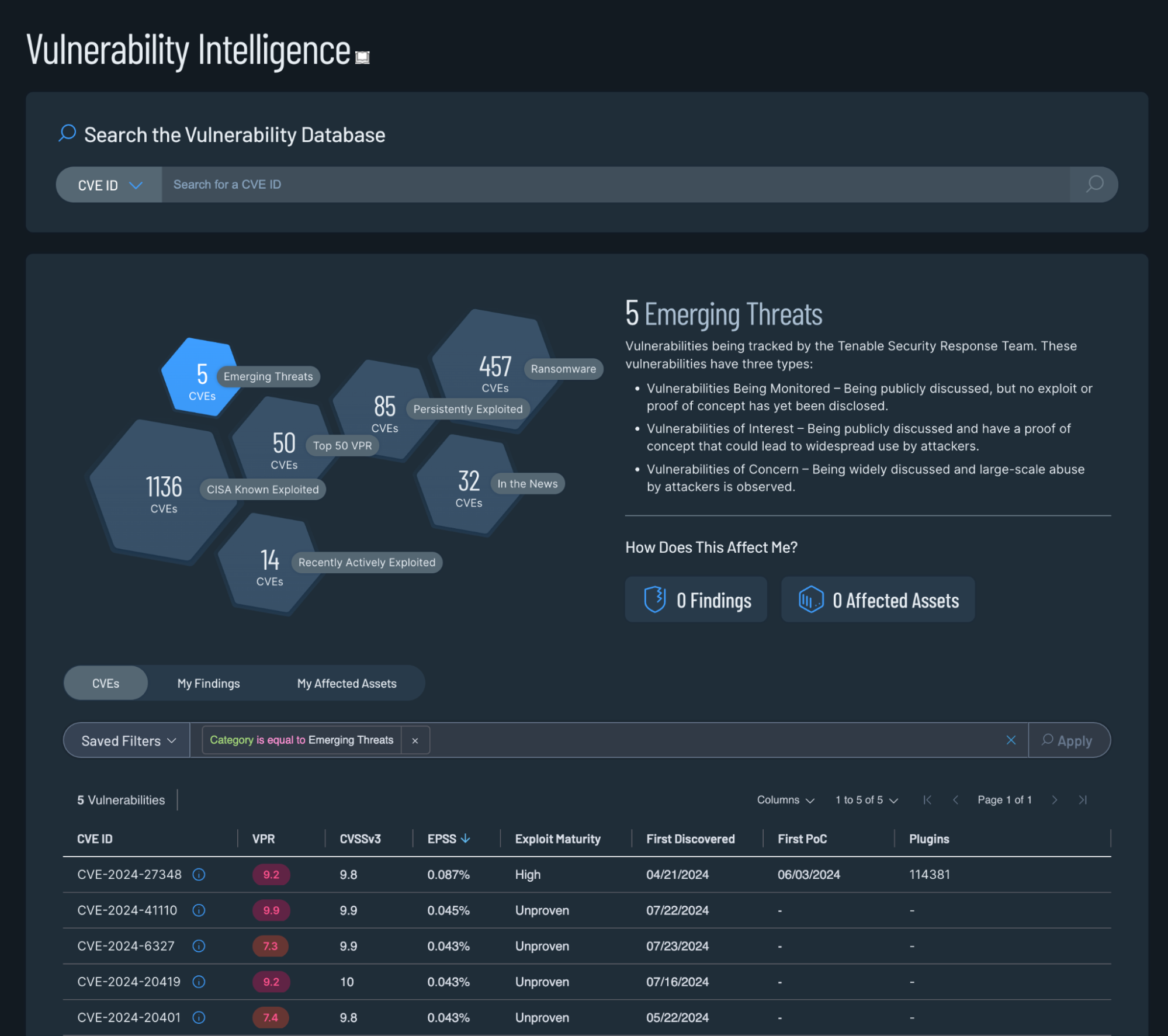
Nach dem Öffnen von Tenable Vulnerability Intelligence wird eine Reihe von Sechsecken angezeigt, die Risikokategorien von Schwachstellen darstellen, die wir als besonders bedrohlich hervorheben möchten. Die Kategorien in Tenable Vulnerability Intelligence sind zwar nicht die einzigen Entscheidungskriterien, basieren jedoch auf Datenpunkten, die in die Tenable Vulnerability Database einfließen, die wiederum die Grundlage für unsere Entscheidungen zur Risikobewertung bildet.
Zu den Kategorien gehören:
- Neuartige Bedrohungen („Emerging Threats“) sind eine Reihe von Schwachstellen, die von unserem Security Response Team aktiv überwacht werden und bei denen es oft einen unmittelbaren Weg von diesem Team zur Entwicklung von Plugins gibt, die diese Schwachstellen abdecken. Dies gilt insbesondere für Schwachstellen der Kategorien „Vulnerabilities of Interest“ und „Vulnerabilities of Concern“.
- Das Tenable Vulnerability Priority Rating (VPR) bietet unseren Teams eine numerische Bewertung, die sie schnell eingeben und sortieren können. Wie bei jeder Bewertung ist es jedoch entscheidend, den Kontext hinter der Bewertung zu verstehen.
- Ransomware hebt die mit diesem Angriffstyp verbundenen Schwachstellen hervor, insbesondere in wichtigen Enterprise-Anwendungen, da diese zu Angriffen führen können, die für alle Organisationen besonders gefährlich sind.
Wie im Screenshot oben zu sehen ist, lässt sich die Anzahl der CVEs, die es zu beachten gilt, erheblich reduzieren, wenn Sie sich auf eine dieser Zielkategorien konzentrieren. Im Vergleich zu den etwa 250.000 CVEs, die bisher veröffentlicht wurden, sind die oben genannten Zahlen weitaus überschaubarer und entsprechen entsprechen dem tatsächlichen Risiko, im Gegensatz zu den Schweregraden, die sich aus der Verwendung von CVSS-Metriken ergeben.
Umwandlung von Daten in eine Priorisierungsstrategie
Viele Unternehmen bauen ihre Prozesse immer noch auf grundlegenden Priorisierungsmetriken auf – sei es im Hinblick auf bestimmte Produkte, CVSS-Scores oder proprietäre Vorgaben. Oft liegt dies an der Notwendigkeit, einen bestimmten Compliance-Standard einzuhalten, oder einfach daran, dass man etwas braucht, das gemessen werden kann. Zwar kann die Verfolgung und Messung anhand eines einfachen CVSS-Scores oder Schweregrads recht einfach sein, doch diese Methode bietet kaum Kontext und ist keine Strategie, die eine nachweisliche Wirkung auf das Risiko hat.

Genau hierbei kann die neue Funktion „Exposure Response“ von Tenable Vulnerability Management helfen. Mithilfe von Tenable Exposure Response können Teams Schwachstellenmanagement-Strategien entwickeln, die messbar sind und das reale Risiko widerspiegeln. Eines der wichtigsten Tools in jedem Schwachstellenmanagement-Programm ist die Fähigkeit, die Leistung zu verfolgen. Leider sehen die meisten Diagramme am Ende wie eine flache Linie aus, da die Anzahl neu hinzukommender Schwachstellen die Anzahl der Schwachstellen ausgleicht, die laufend behoben werden. Durch fokussiertere Zielvorgaben ist es möglich, die Leistung im Zeitverlauf wirklich zu messen und erreichbare SLA-Ziele aufzustellen.
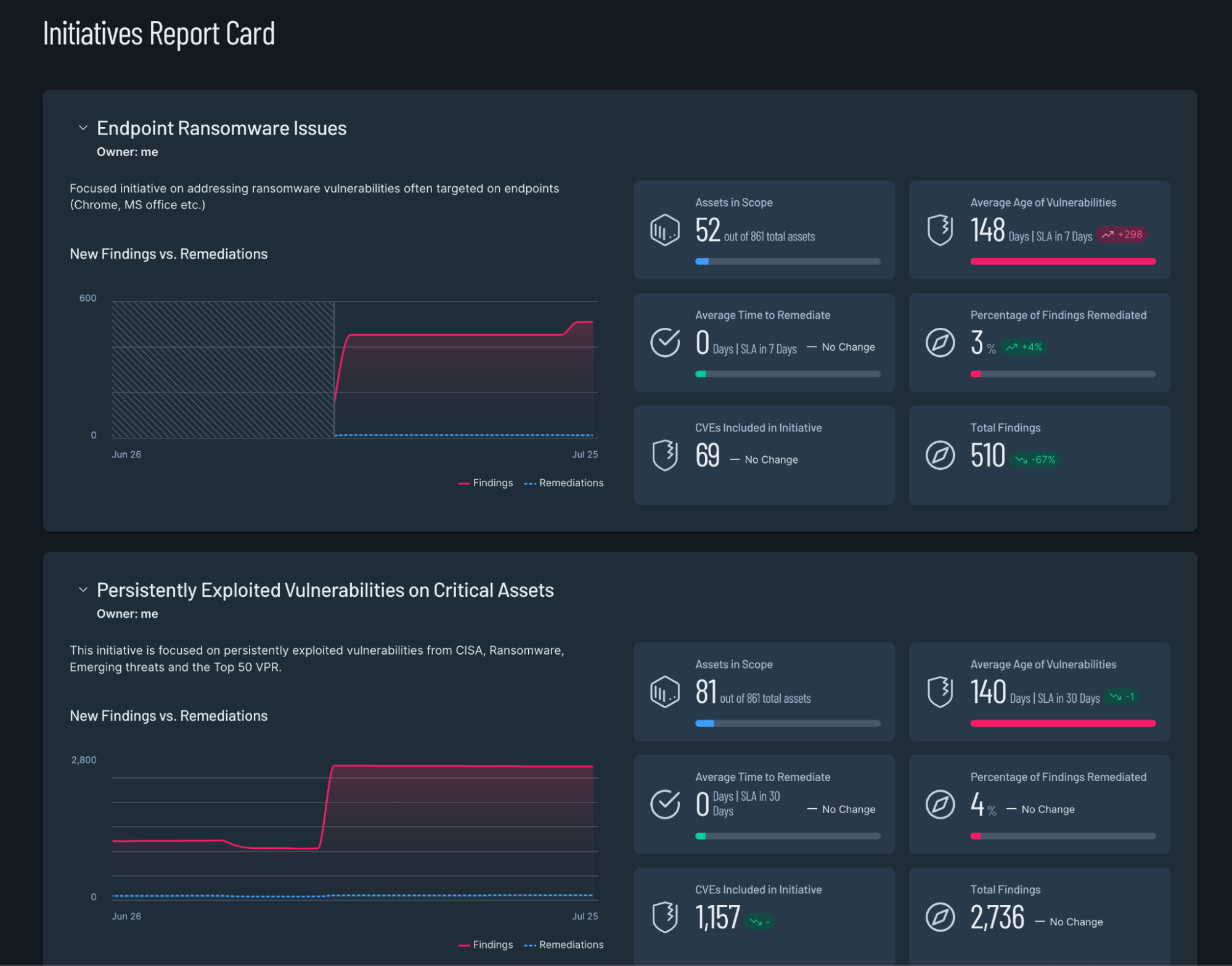
CISA-KEV-Initiativen
Der KEV-Katalog (Known Exploited Vulnerabilities) der US-amerikanischen Cybersecurity and Infrastructure Security Agency (CISA) hat sich zu einer wertvollen und beliebten Ressource entwickelt, die den Fokus auf eine bestimmte Gruppe von Schwachstellen lenkt, die nachweislich in freier Wildbahn ausgenutzt wurden. Obwohl der KEV-Katalog nicht umfassend ist, haben das mit diesen speziellen CVEs verbundene Risiko und die Aufmerksamkeit, die viele Unternehmen dem KEV-Katealog schenken, dazu geführt, dass er einer von mehreren Benchmarks ist, die unsere Tenable Research-Teams zur Verfolgung der Schwachstellenabdeckung nutzen. Mithilfe von Tenable Exposure Response können Vulnerability Management-Teams eine nachverfolgbare CISA KEV-basierte Initiative erstellen, an der sie ihre Behebungsmaßnahmen messen können. Wie bereits erwähnt, sind SLAs und Benchmarks für jede Behebungsstrategie von entscheidender Bedeutung. Wir bemühen uns, so schnell wie möglich eine Abdeckung für KEV-Schwachstellen bereitzustellen, idealerweise noch bevor sie im KEV veröffentlicht werden, aber wenn nicht, dann oftmals innerhalb weniger Stunden nach der Veröffentlichung im KEV.

Tenable Exposure Response bietet genau die Tools, die für diese Art von Messungen benötigt werden. Angesichts der Sichtbarkeit und des Risikos, die mit dem KEV einhergehen, kann es sinnvoll sein, ein SLA von nur wenigen Tagen aufzustellen und einen Richtwert von >90 % behobener Funde anzustreben. Das Wichtigste dabei ist, dass die festgelegten Strategien messbar und realisierbar sind.
Im Gegensatz zu den 250.000 CVEs, die veröffentlicht wurden, befinden sich im CISA KEV-Katalog nur 1134 CVEs. Da jeden Monat nur eine Handvoll CVEs zum KEV hinzugefügt werden, handelt es sich um eine aussagekräftige Gruppe von CVEs, an denen Teams ihre Leistung tatsächlich messen können.
Fazit
Die Priorisierung und Operationalisierung von Schwachstellen ist seit langem eine große Herausforderung für die Teams, die für das Schwachstellenmanagement zuständig sind. Die schiere Menge an Schwachstellen, die Jahr für Jahr veröffentlicht werden, bedeutet, dass Teams einfach nicht mithalten können. Der Mangel an leicht zugänglichem Kontext führt zudem dazu, dass die Priorisierung oftmals entweder ein reines Ratespiel ist, einen enormen Arbeitsaufwand darstellt oder eine begrenzte Anstrengung ist, die zu kurz greift, weil man sich beispielsweise nur auf CVSS-Schweregrade konzentriert. Tenable Vulnerability Management bietet deshalb ab sofort Vulnerability Intelligence, das den gesamten benötigten Kontext an einem zentralen Ort bereitstellt, sowie Exposure Response, um einen zielgerichteten und messbaren Workflow für das Schwachstellenmanagement zu ermöglichen.
Mehr erfahren
- Nehmen Sie an unserem Webinar teil (auf Englisch): From Frustration to Efficiency: Optimize Your Vulnerability Management Workflows and Security with Tenable
- Lesen Sie die Pressemitteilung
- Erfahren Sie mehr über Vulnerability Intelligence und Exposure Response
- Sehen Sie sich die Produktseite von Tenable Vulnerability Management an
Mehr erfahren
- Exposure Management
- Risk-based Vulnerability Management




Tenable One
Demo anfordern
Die weltweit führende KI-gestützte Plattform für Exposure Management
Vielen Dank
Vielen Dank für Ihr Interesse an Tenable One.
Ein Vertriebsmitarbeiter wird sich in Kürze mit Ihnen in Verbindung setzen.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success