Strengthening Cyber Protections in the DoD's OT Systems
Operational technology plays a major role in many aspects of the U.S. Department of Defense — including in military operations, in the infrastructure on bases and throughout the supply chain. Strengthening the cyber defenses of these systems is imperative. Here’s what you need to know.
From managing energy and water resources to streamlining logistical operations, Operational technology (OT) is instrumental in maintaining the effectiveness and readiness of the Department of Defense's (DoD) diverse infrastructure. However, this also presents security challenges, especially considering the increasingly sophisticated nature of modern cyberthreats.
Cyberthreats have significantly escalated in recent years, presenting an ever-growing challenge for organizations, including the DoD. A 2023 report by ISACA revealed that 48% of organizations experienced an increase in cyberattacks compared to the previous year. Meanwhile, a 2023 report from Cybersecurity Ventures forecasts that cybercrime will result in damages totaling $9.5 trillion in 2024— an amount that would equate to the world's third-largest economy, only behind the U.S. and China. Securing OT will ensure the DoD can focus on its mission.
The role of OT in military operations
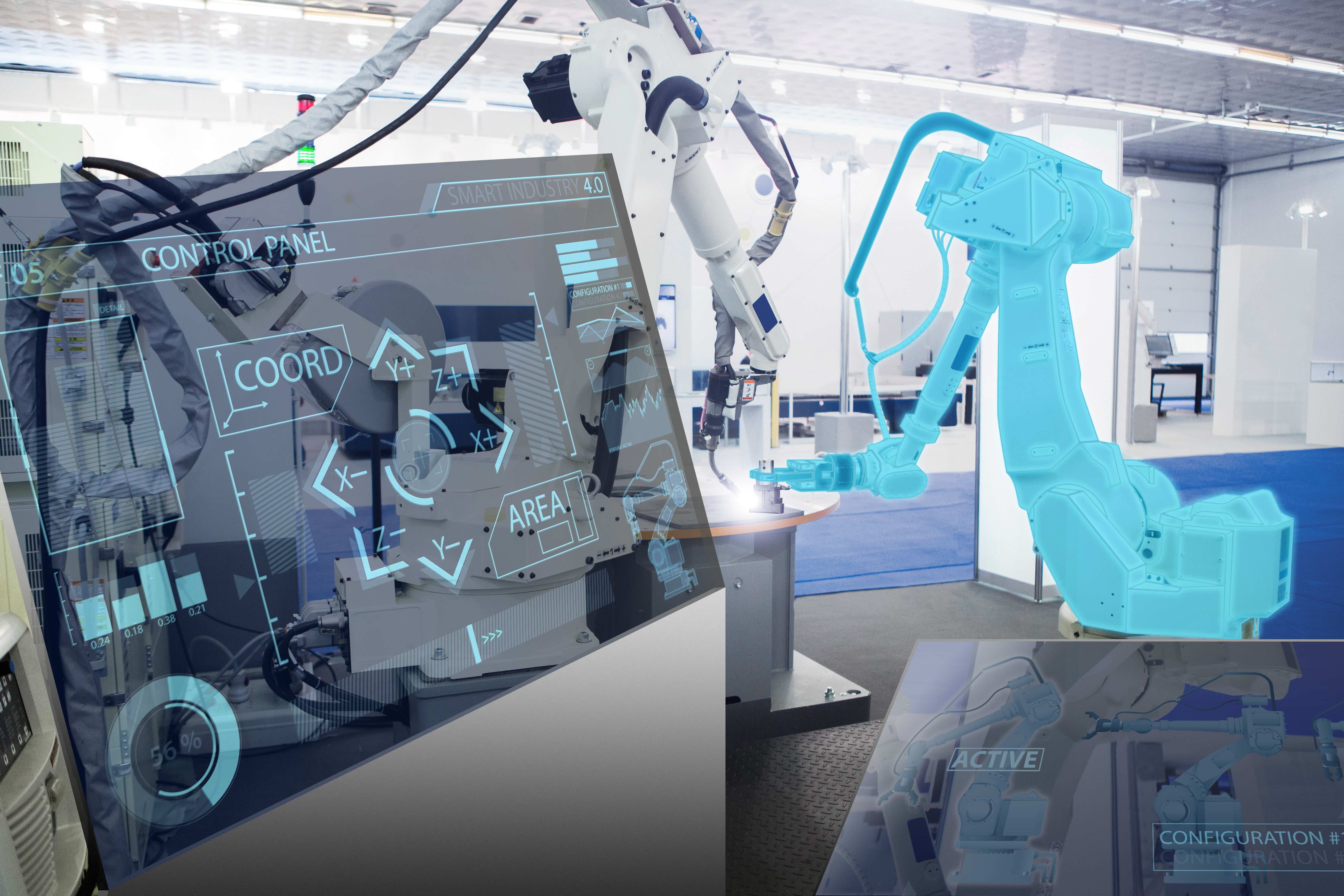
OT is used to connect industrial devices, such as robots and sensors, that assist in the continuous operation of equipment and devices. Unlike traditional IT systems, OT is directly involved in the monitoring and controlling of physical processes and systems that help improve efficiency, decrease manual labor and enhance safety. For military installations, OT plays a pivotal role in automating and enhancing operations across various domains, such as:
- Energy management: OT is integral in operating power plants, integrating renewable energy systems and monitoring power use.
- Logistics support: OT systems are key in managing transportation networks and ensuring efficient supply chain operations.
- Infrastructure reliance: Water treatment and building management systems rely heavily on OT to function smoothly and efficiently.
Each installation is like a miniature city, with its unique infrastructure and requirements, presenting a diverse set of security challenges and needs for OT security solutions.
Legislative context and zero trust
Underpinning the urgency to secure OT systems is the legislative landscape. The National Defense Authorization Act and the DoD Zero Trust Strategy mandate a fortified cybersecurity posture for OT technology. These regulations aren't mere guidelines but essential frameworks directing the path toward comprehensive cyber-physical defense. They establish legally binding standards and practices, ensuring that cybersecurity measures are not only consistently applied across the DoD but also adapted to evolving threats. This is intended to help safeguard national security and the integrity of critical defense operations.
Where OT is used in the DoD
OT is not only instrumental in day-to-day operations but also plays a significant role in enhancing the DoD's readiness and responsiveness.
Here are a few areas where OT is found on military installations, along with the unique challenges that using OT brings to each:
Base energy management: Military bases require an uninterrupted power supply for operations like communications and surveillance. OT systems play an important role in managing and monitoring power distribution, ensuring not just efficiency but also reliability.
The paramount challenge lies in protecting the OT systems managing power distribution from cyberattacks, as any breach could not only disrupt operations but also compromise the security of the entire base.
Logistics and supply chain management: The DoD relies on effective coordination for the movement of equipment, supplies and personnel. OT automates and streamlines these logistical processes, from inventory management to transportation.
A security breach in these OT systems could lead to significant delays and resource losses, impacting military readiness and operational success.
Naval operations: Particularly on vessels operating in strategic or hostile environments, naval operations depend heavily on secure and reliable communication systems. These systems, integrated and supported by sophisticated OT networks, ensure robust and uninterrupted communication, including satellite and onboard communications.
Cyber intrusions could disrupt operations and compromise the safety of a vessel and its crew.
High-security military installations: With their need for stringent access control, surveillance and facility management, high-security military installations rely heavily on OT. These systems manage everything from heating, ventilation and air conditioning (HVAC) systems to security checkpoints, ensuring the smooth functioning of facilities and the safety of personnel and assets.
Protecting high-security systems from cyber intrusions helps maintain both smooth functioning and the safety and integrity of high-security areas.
Automated defense systems: Used for a range of purposes including missile defense and drone operations, automated defense systems underscore the importance of OT in modern warfare. These systems, relying on real-time data and control mechanisms, are pivotal for effective defense and threat response.
Ensuring these critical defense OT systems operate as intended and remain impervious to enemy compromise is vital for national security.
Keeping OT secure
A comprehensive cybersecurity solution keeps OT systems secure and running optimally. The ideal solution integrates seamlessly into the DoD's existing systems, complies with federal mandates and prepares DoD users for cybersecurity readiness. The integration must also ensure a comprehensive security posture — addressing the vulnerabilities of OT environments without hampering efficiency or reliable performance.
The ideal solution for keeping OT secure, includes:
- Comprehensive asset discovery: A thorough approach to identifying and monitoring every component within the OT network.
- Proactive vulnerability management: Continuously monitoring and mitigating security threats to maintain a fortified defense.
- In-depth network traffic analysis: Providing early detection of security incidents through meticulous monitoring of network traffic.
- Network segmentation and access control: Implementing robust network segmentation to minimize the attack surface and control access to critical systems and data.
- Incident response and forensics: Equipping teams with tools for effective incident response and forensic analysis, enabling swift action and in-depth investigation of security incidents.
- Compliance and reporting: Comprehensive reporting to support compliance with relevant regulations and standards, providing clear visibility into security posture and compliance status.
The future of DoD's OT security
The security of OT systems is not just a matter of operational integrity but a critical factor in maintaining national defense and military readiness.
As cyberthreats continue to evolve, so does the need for OT security measures. Tenable OT Security addresses the challenge head-on with its patented hybrid discovery approach, designed to safely gain visibility into devices and cyber-physical systems without disruption. It delivers a comprehensive asset inventory and deep situational awareness across global sites via a single interface. Tenable OT Security helps users prioritize cybersecurity actions and facilitates better collaboration between IT and OT teams. With Tenable, the DoD can significantly enhance its resilience and operational readiness while protecting OT systems in a shifting landscape of cyber threats.
For a deeper look into operational technology for the DoD, read our whitepaper, 5 OT Security Use Cases for the DoD. The Tenable team is also available to provide a demonstration of Tenable’s solutions and show how they can help secure the future of defense operations. Please visit our Tenable OT product page to learn more and request a demo.
This is the first blog in our six-part blog series on OT in the DoD. Below are links to other blogs in the series:
- Keep the Water Flowing for the DoD: Securing Operational Technology from Cyberattacks
- Protecting DoD Building Management Systems with Advanced OT Security
- Enhancing Transportation Cybersecurity and Fleet Management for the DoD
- Navigating Security Challenges Around OT in the DoD’s Manufacturing Lines
- Operational Technology in the DoD: Ensuring a Secure and Efficient Power Grid
Learn more
- Federal
- Government
- OT Security




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success